5 Questions to Help SMEs with Their Cyber Security
SMEs make up 99% of UK businesses, three fifths of employment, over 50% of all business revenue, are in everyone's supply chain, and are exposed to largely the same threats as large enterprises. How should they get started with cyber security?
Small and Medium sized Enterprises (SME) are not immune to the threat of cyber attacks. At the very least, if your business has money then it will be attractive to criminals. And even if you don’t have anything of value, you may still get caught up in a ransomware campaign with all of your data and systems made inaccessible.
Unfortunately many SMEs do not have an IT team let alone a cyber security team. It may not be obvious where to start, but inaction can have significant impact on your business by both increasing risk and reducing the confidence to address new opportunities.
In this article we outline 5 key questions that can help SMEs to understand what they need to do. Even if you outsource your IT to a supplier these questions are still relevant. Some can’t be delegated, and others are topics for discussion so that you can ensure your service provider is doing the right things, as well as understanding where their responsibilities stop and yours start.
Q1: What's Important & Worth Defending
Not everything needs protecting equally. In your personal life you will have some possessions that are dear to you and others that you are more laissez-faire about. The same applies to your digital assets, and the start point for any security plan needs to be an audit of the things you own and their importance to your business.
Those ‘things’, or assets, may be particular types of data or information. For instance, you may have sensitive intellectual property or trade secrets; you may hold information about your customers that is governed by privacy regulations; or your financial data may be of particular concern. Some of this information needs to be protected from theft, while it may be more important to prevent other types of data from being modified or deleted.
It is helpful to build a list of these assets, and their characteristics like the table below:
| REF | Name | Description | Impact | Where | Sensitivity |
|---|---|---|---|---|---|
| 1 | Finances | Accounting and financial planning documents | If modified or deleted we would be unable to produce accurate reports for tax and may fail to meet customer contractual obligations. | Xero Finance SharePoint Accountants | Very High |
| 2 | Product IP | Product designs, future feature roadmaps, source-code | If stolen we would lose competitive advantage. If modified defects or vulnerabilities could be inserted causing our service to malfunction or putting our customers at risk. | GitHub Cursor All | High |
| 3 | Customers | Customer registration and order details | If stolen we would lose customer confidence and may be subject to fines and/or lawsuits. If modified we may be unable to meet customer contractual obligations. | HubSpot Sales SharePoint Email | High |
| 4 | Employees | Employee records including payroll and tax details | If stolen we would put our employees are risk and may be subject to fines and/or lawsuits. If modified or deleted we may be unable to pay our employees on time. | Xero HR SharePoint | High |
| 5 | Marketing | Future marketing plans, market segmentation data, campaign content and plans | If stolen we may lose competitive advantage. If marketing content was modified it could damage our reputation, put our customers at risk, and may lead to lawsuits. | Website Marketing SharePoint | Medium |
You may also have other assets that are critical systems your business couldn’t operate without. For example, you may have a computer controlled manufacturing system and would start losing significant revenue if it stopped working for more than a week.
This asset list is unique and personal to your business. This isn’t something that can be delegated or outsourced to an IT service provider. They will most likely be unaware of the assets you use, and will certainly be unable to assess their criticality to your business. By spending some time developing this asset register you will be in a better position to decide what needs protecting and to what extent.
Q2: Are Your Users' Accounts Being Protected?
Your employees need to be able to access your assets in order to do their jobs. You finance staff need to access financial data, and your marketing team needs to be able to work on their campaigns. But because they can usually access sensitive data, if those user accounts were hijacked this same data will be fully accessible to the bad actor as well. This is why its so important to reduce the likelihood that anyone other than a genuine user can access their account.
The basic starting point is to make sure that your staff choose difficult passwords, don’t share them with anyone else, and never use the same password for different services. These rules will largely rely on a policy that you educate your staff to follow. But the single greatest improvement you can make to this aspect of security is to enable Multi-Factor Authentication (MFA). Sometimes called Two Factor Authentication (2FA) or Two-Step Authentication, this forces the individual not only to enter their password but also a one-time code that they might get by text message or from an app on their phone. It means that they are confirming their identity not only with something they know – the password – but also with something they have – their phone that is receiving the text or has the app installed.
The measures described above will strengthen authentication, increasing the confidence that the correct person is using an account and that it hasn’t be hijacked. But it is also important to make sure people only have the permissions they need to do their job. Limiting access to sensitive information further reduces the risks that it will be compromised if an individual account is broken into.
While an IT service provider may be able to put some of the authentication controls. But controlling who can access or change what – the authorisation part of the equation – is a business decision. While the execution might be delegated the decision making cannot.
Q3: How Secure Are Your Devices?
Your devices should, obviously, have anti-virus or anti-malware software installed, and up-to-date, to reduce the likelihood malicious code can be loaded or be able to run. But it has been a long time since this alone was sufficient to keep you even moderately safe.
Any software will have defects. When an application consists of hundreds of thousands or millions of lines of code, it is inevitable that mistakes will have been made. Some of these defects are weaknesses or vulnerabilities that an attacker can exploit to gain illegal access or control of the system. Every day new vulnerabilities are discovered in software. Sometimes they are discovered and reported by honest people as a result of their research and testing. But frequently they are only uncovered when a bad actor has exploited them to cause damage to an organisation.
The good news is that as vulnerabilities are discovered, the more reputable software companies work hard to update the code to remove them. If you always have the most up-to-date software running on your laptops, mobile phones and other devices then the risk of being attacked via a vulnerability is reduced significantly. Some of can be set to update automatically. The operating system, most web browsers, and many other pieces of software will regularly check for new versions and install them. But you need to ensure this feature is enabled. You also need to ensure that any obsolete software that is no longer being supported is removed, because no updates will be provided for new vulnerabilities when they are discovered.
Some software vendors are better than others at addressing vulnerabilities. For this reason it is important to make a conscious decision about what applications people can install on their devices and use for business.
A lot of the tasks described in this section can be made easier, with automated warnings and reports, by using additional tools or services. For instance, a Mobile Device Management (MDM) service – such as Microsoft Intune or Endpoint Management in Google Workspace – can enable you to manage all of the devices in your business and ensure that they are configured correctly. Similarly, a Vulnerability Scanner running on devices will alert you when devices running vulnerable software.
If you outsource your IT then most of the tasks described should be the responsibility of your service provider. But the risk will ultimately impact on your business, so it is important to ensure they are following good practice.
Q4: What If Your Assets Are Stored in the Cloud?
Increasingly your assets will be stored and processed in cloud services. This might be a single-purpose Software-as-a-Service (SaaS) application, like HubSpot CRM or Xero financial management. Or it could be broader cloud service, like Microsoft 365 or Google Workspace. You might also have other suppliers who process your data or interact with your systems. Regardless of the scope and scale, you will first need to decide whether you trust the vendor to protect your information that is in their custody.
The level of trust you need should be proportionate to the value of the asset, just as it is in the physical world. When you hand your clothes over to a dry cleaner you might want confidence that they will not damage them in the process, but may be comfortable receiving compensation if they do. But when you are selecting a child-minder you are likely to conduct significantly greater due-diligence before entrusting them with your child because the consequences of failure are significantly greater and compensation will offer little comfort. Conducting appropriate due diligence over suppliers who are handling your data may not be simple, but where the impact of things going wrong is high then it is an important task.
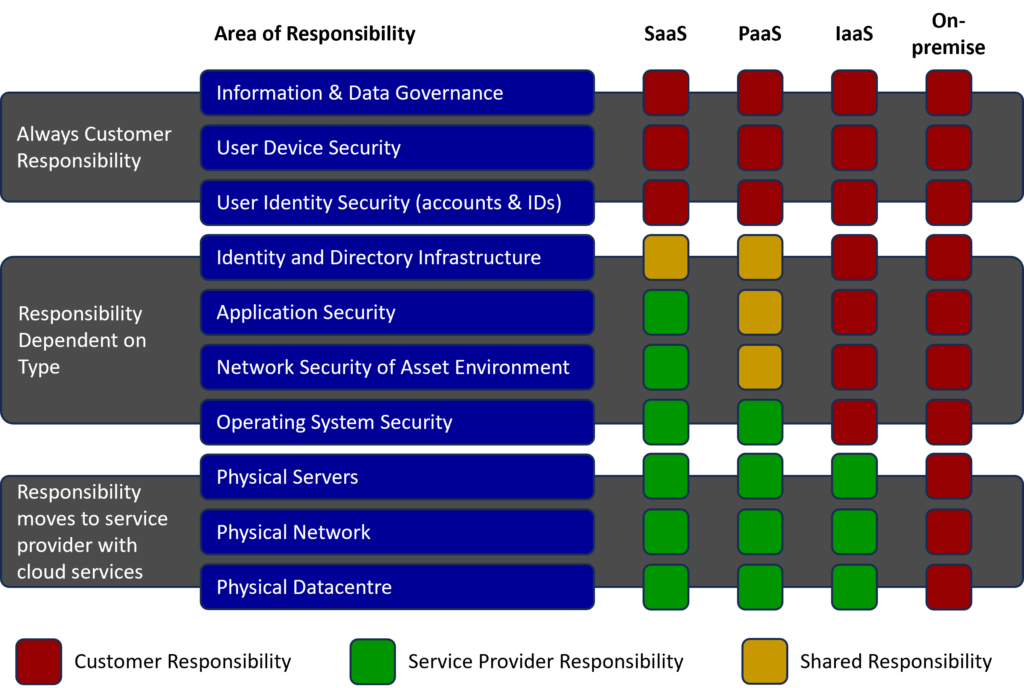
With cloud services the responsibility for security is shared between the customer and the service provider. For instance, the service provider is responsible for ensuring there is a secure method for users to log into the system, and that your data cannot be accessed by someone who has not logged in with the correct rights and permissions. But as the customer, it is your responsibility to make sure you only give access and permissions to the people who need it. It is also your responsibility to ensure your users don’t choose a simple password, or share it with anyone, and to enable MFA if that is available. The diagram below outlines where responsibility falls for the majority of cloud services.
Q5: What Connects to What?
Having gone into the issues outlined so far it would be a shame to then leave the back door open. Would you invest in a strong front door with a five lever lock and covered it with CCTV if your side door was only secured with a £5 Yale Lock. In the digital world, we are presented with a dizzying array of different applications that can make our life easier by integrating with each other. This is particularly the case with the cloud SaaS applications, where we can often connect one service to another at the click of a mouse.
You might connect your CRM to your email service so that it tracks the interactions you are having with individual customers. Or you might connect a reporting and analysis service to your financial management application. But each time you connect two services together you are opening up a new route to the asset. In the first example, your email service might be highly secure, but if the CRM service is insecure then the bad actor can get to your data that way.
Risk is a balancing act. There will always be risk, but the objective is to balance the benefit that you get against the risk that it introduces. Returning to the CRM example, you might allow members of your sales team to integrate it with email because the business benefit is significant, but not your executive team because the risk is not justified.
Another area of integration risk that is frequently overlooked is the use of browser extensions. These little apps that can be installed into the browser might block advertisements, offer a convenient dictionary or calculator, or provide a short cut for a particular website. But whenever you install an extension you are giving it certain permissions, and bad people can publish extensions as well as good people.
Conclusion
Good security is never done, and is best approached as an ongoing task. The five questions above are intended as helpful guidance rather than a comprehensive approach. But the important thing to do is to get started. Over time you can progressively improve your security and reduce your risk. In turn this can give you confidence to be bolder in the marketplace and to address opportunities that you previously felt were out of your reach.
If you want to discuss how you can improve your security, reduce your digital risk, and face the future with confidence, get in touch with Tom Burton, Senior Partner - Cyber Security, using the below form.
Contact - SME Cyber Security article
Subscribe to our Newsletter
Blog Subscribe
SHARE CONTENT












