Making Waves: How Subsea Cables are Improving Global Connectivity
In 2011, the United Nations (UN) declared their Broadband Advocacy Targets, in which they promised to Make Broadband Policy Universal by 2025. Given that over 90% of all internet traffic passes through submarine cable systems, such networks have become a hugely influential factor in this goal, and thus a significant global and political force.
Since the inception of telegraph cables in the mid-to-late 19th century, the prevalence of geopolitics in the submarine cable industry has been intrinsic and impossible to ignore. It is no coincidence, after all, that the current network of cables traces the same lines as the original trade routes: both possess the shared purpose of connecting multiple regions across numerous continents in the shortest time – to boost economies and promote international directives. The telegraph cables of the British Empire were exactly that, a way to consolidate power and trade throughout vast geographical distances.
Thus, as we come rapidly closer to the UN’s 2025 target, this article will focus on the positive impacts which are created and accelerated by access to undersea connectivity. In doing so, we will explore different regions, how they are currently benefitting from the UN’s path toward a more connected globe, as well as opportunities for improvement on the horizon.
Repeatered Cables
Before going into greater detail on the regions that current subsea networks traverse, and the positive impacts they bring, it is worth hovering briefly on the technical make-up of these cables, particularly the component of ‘repeaters’. Also known as optical amplifiers, repeaters are present at intervals along submarine cables which are longer than several hundred kilometres (as opposed to those used within lakes or rivers, etc.) and are built within the ocean floors, often several kilometres deep. Given the length of these cables, repeaters are used to amplify information-carrying wavelengths to sustain the quality of received optic signals over such long distances.
However, given their housing in such a harsh and inaccessible environment, redundancy – the technical term for having a backup or recovery option for failed or damaged subsea cables – becomes crucial. Repairing repeatered submarine fibre cables can be incredibly capital intensive and complex, and thus it is important to ensure the strength and stability of subsea cable networks to protect the longevity of the benefits outlined below.
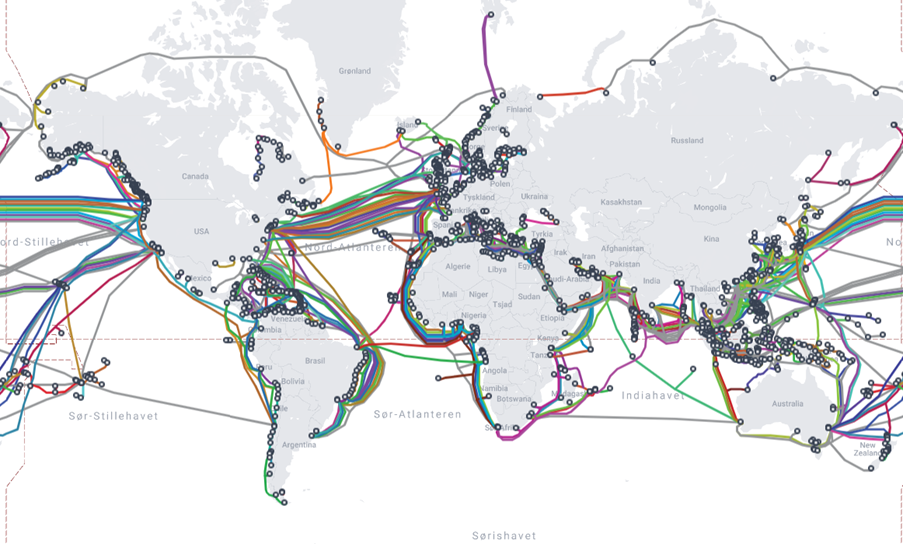
© Telegeography 2024
Africa
Africa is no stranger to the importance of subsea connection, nor the debilitating impacts of a lack thereof. In 2017, Somalia suffered three weeks of internet outage when its only international cable was severed by an anchor, costing the country $10m a day until its repair.
According to a 2023 report from Telegeography, international bandwidth has been doubling every two years, and much of this growth has been concentrated in Africa; the report reveals, ‘Africa experienced the most rapid growth of international internet bandwidth, growing at a compound annual rate of 44% between 2018 and 2022.’ Despite this, less than half of Sub-Saharan African regions – 36% to be exact – are connected to the internet.
This leaves the majority of the region lacking many of the benefits provided by submarine connectivity, including global collaboration and cultural exchange facilitated by the flow of data, as well as more crucial factors such as economic growth and access to education and telemedicine.
As such, Meta has installed a 37,000km cable between Europe, Africa, and the Middle East, named the 2Africa cable. With 16 fibre pairs, this network will connect France, Spain, Portugal, and Italy with 18 countries across Africa and the Middle East. By their own admission, access to reliable connectivity of this kind catalyses entry and expansion into new markets, citing a World Bank Study which highlighted a 1.2% point increase in GDP initiated by a 10% rise in broadband penetration across 66 countries. Thus, the 2Africa cable presents unignorable opportunities and positive impact to the African continent.
It is not only Meta who is expanding their subsea connectivity to Africa, as Google has also extended their cable systems to the continent through two networks: Equiano, named after Nigerian-born writer and abolitionist, Olaudah Equiano, and Umoja, the Swahili word for unity. Equiano connects Westen Europe with the West Coast of Africa and is the first subsea cable system to incorporate optical switching at the fibre-pair level, as opposed to the traditional approach of wavelength-level switching. Similarly innovative, the Umoja subsea cable is the first fibre-optic route to directly connect Africa with Australia. Google’s subsea cable systems are all privately built, allowing them the freedom to choose routes with low latency, tailor bandwidth to their desired customers, and guarantee connectivity with a substantial longevity for them to plan ahead confidently and securely.
Other privately-built subsea ventures traversing Africa include:
- DARE1: Standing for the Djibouti African Regional Express 1, DARE1 connects Djibouti with Somalia and Kenya. Developed by SubCom, this amounts to nearly 5,000km, and supplies up to 36 Tbps of capacity to East Africa.
- PEACE: The Pakistan & East African Connecting Europe (PEACE) cable system is a 15,000km cable spanning between Pakistan and France, as well as an additional 6,500km extending to Singapore. This is owned by Peace Cable International Network Co., as well as having numerous other privately-owned companies using PEACE to leverage their own connectivity from Africa to different regions. (A full list of which can be found here.)
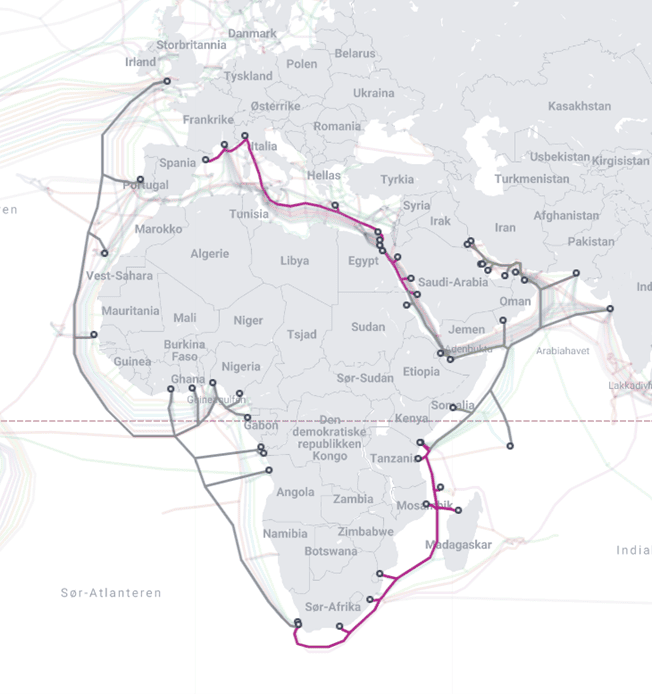
© Telegeography 2024
Asia & the Asia Pacific
According to the same Telegeography report, Asia was a close second to Africa for experiencing the most rapid growth in international internet bandwidth, having risen at a compound annual rate of 35% between 2018-2022. However, similarly to Africa, this is not the case across the entire continent, as South Asian regions find themselves particularly lacking in connectivity. As of 2022, only 43% of users in this region had access to broadband, with Bangladesh and Pakistan home to only two landing stations each compared to Singapore’s 26, despite possessing far larger coastlines, populations, and bandwidth demands.
With Singapore’s already substantial network of submarine cables expected to double by 2030, the country represents one of several highly developed hubs within the continent, accompanied by Japan and Hong Kong. As such, Meta has made it their mission to open these bottlenecks, diversify routes, and reach underserved communities, by developing eight new submarine cable systems with key regional and national partners throughout the Asia Pacific region. Two of these, Echo and Bifrost, will bypass the Luzon Strait – an area which, as aforementioned, is vulnerable to geological events – and are the first to directly connect Jakarta, Indonesia, with the US.
With Meta’s eight new routes set to be completed next year, these initiatives are expected to:
- In Indonesia, increase GDP by $59bn cumulatively and create up to 1.8m new jobs in construction, telecommunications, finance, healthcare, IT, and education.
- In the Philippines, increase GDP by $34bn cumulatively and create 380,000 new jobs.
- Create up to 3.7m new jobs in total across the APAC region.
As these initiatives facilitate the rapid expansion of cloud infrastructure and deployment of artificial intelligence, countries within the Asia Pacific including China, India, and Australia are emerging as epicentres within our technologically transformative age.
Latin America
As with other continents, countries within Latin America are increasingly in demand for stronger and more improved bandwidth. As their largest country, Brazil is in particular need of the connectivity which subsea cable networks provide and is positioned to benefit greatly from its positive impacts, including reduced latency – a prescient concern since the COVID-19 pandemic moved many businesses and their operations online – and access to disaster recovery, given that subsea cables provide redundancy and backup sources of communication in the event of network failures.
As such, EllaLink is working to improve connectivity between Latin America and Europe, positioning Brazil as an epicentre within this network. According to EllaLink, this directive is designed to support ‘economic growth, technological advancement, and social development’, and benefit various sectors including ‘finance, education, healthcare, and entertainment, fostering greater innovation and collaboration across continents.’
As part of this project, Brazil has agreed to remain a neutral partner in the way they control and delegate this connectivity, ‘ensuring that [they do] not favour any particular nation or political agenda’. This underscores the political currency that subsea cables and their connectivity can hold and ensures a step in the right direction that Brazil is committed to wielding it equally and judiciously.
Google has also extended its portfolio of privately-owned subsea cables to Latin America, through the development of Firmina and Curie. Continuing their theme of naming their cables after world-changing visionaries like Equiano, Firmina is named after Maria Firmina dos Reis, a Brazilian abolitionist and author, and runs from the East Coast of the United States to Las Toninas, Argentina – the longest cable in the world capable of running entirely from a single power source if its other power source(s) become temporarily unavailable.
Curie, named after scientist Marie Curie, is the first subsea cable to land in Chile in nearly two decades. Being privately owned allows Google to tailor Curie’s deployment and routing for the optimal latency and availability, including a further branch delivered to Panama, as well as an added layer of security.

© Telegeography 2024
Europe
As well as working to enhance Latin America’s burgeoning connectivity, EllaLink’s subsea cable network is designed to improve Europe’s much-needed access to global connectivity, given that much of the world’s traffic does not yet pass through the continent. To achieve this, EllaLink’s cable will pass through Portugal, one of the more strategic locations within Europe’s geography due to its safety, position, and advanced infrastructure. This relationship will prove to be symbiotic, facilitating cross-continent connectivity while equipping Portugal to attract major technology players and evolve it into a technological hub.
It is not only Portugal in which the benefits of increased connectivity are being concentrated, as Meta’s transatlantic cable system, Marea, has seen an increase of $18bn to Europe’s GDP each year since 2019, equating to roughly 6% of its current average annual growth. Furthermore, they are set to expand these efforts, planning the delivery of two new cables throughout Europe by 2027 which will contribute ~$65bn annually to the European economy.
These subsea cable systems represent several of a portfolio of ongoing and impending network projects being disseminated throughout Europe, with others including:
- Finland: In Finland, the domestic data centre industry is facilitated by the C-Lion1 submarine cable system which connects their capital, Helsinki, with Rostock in Germany. This has the potential to enable an annual economic contribution of €2.3bn and support 33,000 jobs through its data centre industry and supply chain impacts.
- England: A study by the ECB revealed that a large number of the international cables positioned in the UK increased the number of financial transactions by as much as one third, strengthening its position as a financial centre.
- Ireland: Ireland’s existing portfolio of data centres, which are supported by a network of subsea cables, have already generated €7bn between 2010 and 2018, and created 5,700 jobs in construction and operations. Further to this, Meta’s cables in Ireland are estimated to contribute $2.78bn to the Irish economy each year, contributing an impact roughly equivalent to 15% of their typical GDP growth.
- Norway: A report commissioned of Copenhagen Economics by NORDUnet concluded that an Arctic cable could boost GDP in the Nordic region by more than €1bn, not only to investors but more widely to society as a whole. This is enhanced by Norway’s unique conditions, of which its low temperatures and access to renewable energy sources make data centres more energy effective and they emit less CO2 than in other European regions.
- Plans to capitalise on these conditions include Far North Fibers’ delivery of the first ever long-haul submarine fibre route through the Arctic Ocean, connecting Asia to Europe via the Northwest Passage. This is partly fuelled by the increasing demand for international data transmission and Internet of Things (IoT) adoption, as well as the approaching expiry date of current trans-ocean fibre optic systems, which are gradually reaching the end of their design lives – an important consideration given the repair difficulties outlined previously. Also, while the Arctic, in terms of ice, creates a challenge, the planned cable is very secure as the ice protects the cable for most of the year.
- Furthermore, Space Norway is preparing to implement a new fibre cable connecting mainland Norway to Svalbard by 2028, after one of the previous two cables was damaged in 2022.
North America & the North Atlantic
As well as this array of subsea projects designed to boost connectivity within Europe, there are several further ventures seeking to enhance this through connection with North America specifically, as well as neighbouring geographies in the North Atlantic.
One such network is the Anjana cable system, another Meta-led endeavour which will connect Myrtle Beach in South Carolina to Santander in Spain via over 7,000km of transatlantic fibre-optics. Expected to be delivered by the close of this year, the Anjana cable is set to be the highest-capacity subsea cable in the world, overtaking Google’s UK to US Grace Hopper cable, and providing the first landing station in Santander. As such, it will respond to both Spain and South Carolina’s growing need for geographic diversity and network resilience through improved user experience, redundancy, and scalability.
As well as this, Google is seeking to connect the US with Bermuda, the Azores, and Portugal, through a subsea cable network named ‘Nuvem’ – the Portuguese word for ‘cloud’. Nuvem will be the first cable of its kind to connect Bermuda with Europe, following the Government of Bermuda’s work to encourage investment in subsea cable infrastructure, including the introduction of legislation to create cable corridors and simplify the permitting process. This highlights the desirability of subsea cables, and Nuvem will respond to Bermuda’s objectives through the creation of trade, investment, and productivity.
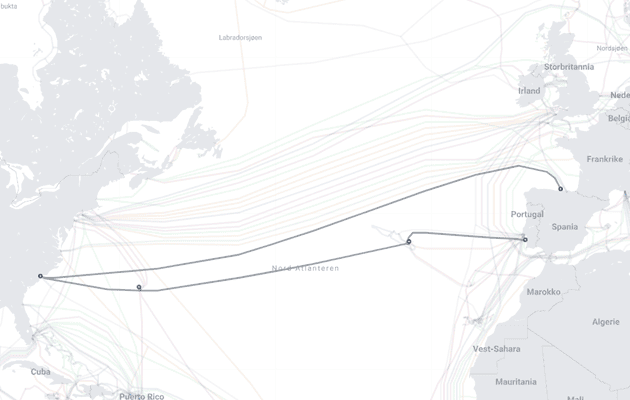
© Telegeography 2024
Cambridge Management Consulting's Subsea Projects
It is clear from this top-down view of the subsea network industry that the power and importance held by cables which are often no thicker than a hosepipe cannot be overstated. Transmitting over 90% of all data traffic, their influence on the economies, infrastructure, and opportunities for collaboration is present in the significant growth they create in each region they connect. In short, though they may be hidden deep below sea level, their presence is felt palpably in the fabric of every society.
This presence is something we at Cambridge Management Consulting are striving to amplify. Our Subsea Infrastructure team, within our Telecoms, Media, and Technology service, is equipped with combined decades of experience in the planning, research, and delivery of subsea infrastructure. Examples of this work include:
- Aki Uljas, C-LION1 & C-LION2: Senior Partner and lead for Subsea, Aki Uljas, was engaged by Cinia to be responsible for the technical and commercial development of their implementation of the C-LION1 submarine cable system in the Baltic sea. For this project, Aki led the site selection and design of cable landing stations, as well as the overall network design. Following this, Aki is currently providing advisory services to Cinia’s subsequent subsea project, C-LION2, which is similarly providing connectivity to the Baltic Sea region. In addition, Aki Uljas has developed a cable system between Europe and Japan, via the Arctic Sea, now called Far North Fiber.
- Erling Aronsveen, Celtic Norse: From 2018 until present, Erling Aronsveen, Senior Partner for Nordics, has been developing the Celtic Norse submarine fibre-optic cable system, planned to extend from Killala Bay, County Mayo, Ireland, to Trondheim, Norway. This cable system is a joint venture between three Norwegian Energy Companies, also including Eidsiva and Aqua Comms Ltd., Ireland. This is the first system of its kind connecting Norway and Ireland, and provides further connectivity to the US, allowing Norway to break into the hyperscale and enterprise data centre market.
- Andy Bax, Seabras-1: In 2007, Andy Bax, Senior Partner for Digital Infrastructure, began leading the development, design, and implementation of a new 1,240km submarine fibre optic cable system linking Trinidad, Guyana, and Suriname, providing the first direct submarine cable connections to the latter two regions. Further to this, in 2010, Andy led the design, construction, and implementation of Seaborn Networks’ Seabras-1 submarine cable system from New York to Brazil.
- Turks & Caicos: In 2023, Cambridge MC was awarded a contract to prepare the final Strategic Outline Business Case (SOBC) for their proposed domestic submarine telecommunications cable system for the Turks & Caicos Islands (TCI). The primary object of this is to replace the current microwave links with high-capacity fibre optic cables, ensuring resilience connectivity in adverse weather, and offering low latency digital access to underserved TCI communities.
- Cayman Islands: In 2023, Cambridge MC entered into a strategic partnership with the Cayman Islands’ Government’s Ministry of Planning, Agriculture, Housing and Infrastructure to support a critical initiative of submarine cable modernisation. This followed a study which revealed the importance of the Cayman Islands’ existing infrastructure in the context of global connectivity. Cambridge MC’s role in this directive includes project planning, system procurement, and project execution.
Visit our dedicated
Subsea Infrastructure page to read more and learn about how they can support your organisation.
Contact - NIS2 Article
Subscribe to our Newsletter
Blog Subscribe
SHARE CONTENT














