Navigating Change: A Comprehensive Overview of Change Management
In a new series of articles, Daniel Fitzsimmons, an expert in Change Management and Business Transformation, explains the importance of change management to organisations as they evolve and keep apace of technological advances in a rapidly changing business landscape.
What is Change Management?
Change management is a structured approach to transitioning individuals, teams, and organisations from a current state to a desired future state. The primary focus of change management is to help people adapt to change and minimise resistance, ensuring that the desired outcomes of the change initiative are achieved.
Change Management methodologies are grounded in the understanding that the transformation process follows predictable stages, and, as a result, all tasks, efforts, and activities associated with change can be strategically planned, implemented, and success is measured and assessed.
The Cambridge Management Consulting (Cambridge MC) Change Management process places emphasis on creating an environment that supports individuals through the transition and helps them understand the reasons behind the change, the benefits it brings, and how they can contribute to its success.
Our goal at Cambridge MC is to significantly reduce the timeline from project initiation to benefit realisation.
Why is Change Management Necessary?
The statistical reality is that the vast majority of change initiatives fail to achieve the intended results initially outlined for the project. A number of these failings can be linked to over-ambitious targets, however, a significant proportion of these shortcomings can be linked directly to a failure to communicate and effectively operationalise the change initiative with employees.
One of the key reasons why change management methodologies are so critical is its role in mitigating resistance to change across the stakeholder landscape. Stakeholders often feel threatened or uneasy when faced with significant changes in their work environment or processes. This resistance is natural, as it stems from the fear of the unknown and the disruption of established routines.
To address stakeholder resistance and build trust, Cambridge MC places employees at the heart of the change activity, guiding stakeholders on a journey from:

To achieve commitment and ownership of change is no small feat, requiring a conscientious effort to engage employees, not only during the execution phase, but throughout the project and decision-making cycle. Through effective engagement at the outset of the project, Cambridge MC empowers employees (change agents) to take ownership of both the initiative and its subsequent success or failure.
With ownership, however, comes responsibility, and, as such, change leaders must provide change agents with the resources, skills training, and the psychological safety they require to deliver the future of the business.
By implementing a people-centric change management approach, Cambridge MC greatly increases the likelihood of embedding change successfully.
The Role of Managing Change
The significance of change management as a crucial leadership skill has become increasingly apparent, in an era marked by rapid technological advancements, shifting market dynamics, and evolving customer expectations, businesses must constantly adapt and innovate to remain competitive.
As Harvard Business states, “In today’s uncertain climate, leaders at all levels in the organisation are involved in managing change. While senior executives set the organisational tone, those in middle management, leaders on the frontlines, and team leaders also play critical roles.”
Whether driven by external factors like economic fluctuations, industry trends, or internal forces such as mergers and acquisitions, process improvements, or leadership changes, organisations must be prepared to embrace and manage change.
Effective leaders understand that change is inevitable, and, rather than resisting it, they actively embrace it, fostering a culture that values innovation and provides the necessary support and resources to develop solutions to the market challenges being faced. By embracing change, leaders not only steer their organisations towards growth but also cultivate a resilient and forward-thinking team.
Benefits: Three Examples
Mergers & Acquisitions
In the context of M&A, change management is especially critical. Mergers and acquisitions can be highly complex and tumultuous, with significant cultural, structural, and operational differences between the organisations involved. Without effective change management, the risk of post-merger integration failure is high. Change management helps to ensure that the two organisations are integrated seamlessly, with a focus on aligning cultures, retaining key talent, and maximising the synergies that prompted the merger or acquisition in the first place.
Digital Transformation
Change management is indispensable in the implementation of digital transformation programs. Organisations need to continuously adopt new technologies to stay competitive, however, the adoption of technology often involves significant changes in operational governance, workflows, and processes. The development of an environment and operational structure where change is normal, allows organisations to adapt more effectively to change, thereby minimising disruption and maximising the benefits.
Sustainability Programs
Sustainability projects often experience challenges due to a lack of specialist resources, data visibility, and the expertise to align sustainable strategy to business objectives. Leveraging a wealth of industry expertise within a proven framework of change management methodologies, Cambridge MC is uniquely positioned to allow your organisation to maximise the benefits of sustainable operations.
Change management supports the communication of the benefits of sustainability, organisation value alignment, and empowers individuals through training, to facilitate a smooth integration of eco-friendly processes and methods and long-term sustainability goals.
Our Methodology
Change management is not a one-size-fits-all approach, it requires customisation to fit the specific needs of each organisation and its unique change initiative challenges. Effective change management begins with a comprehensive assessment of the current state of the organisation, the desired future state, and the gaps that need to be bridged through the life of the project. Once the assessment is complete, a tailored change management plan is developed, encompassing strategies for communication, training, support, and performance measurement.
Change Imperative: The Reason Why
The Change Imperative is the reason we are having this conversation. Something is compelling the organisation to evaluate its current operations and consider change. These push or pull factors manifest in many forms but necessitate a response:
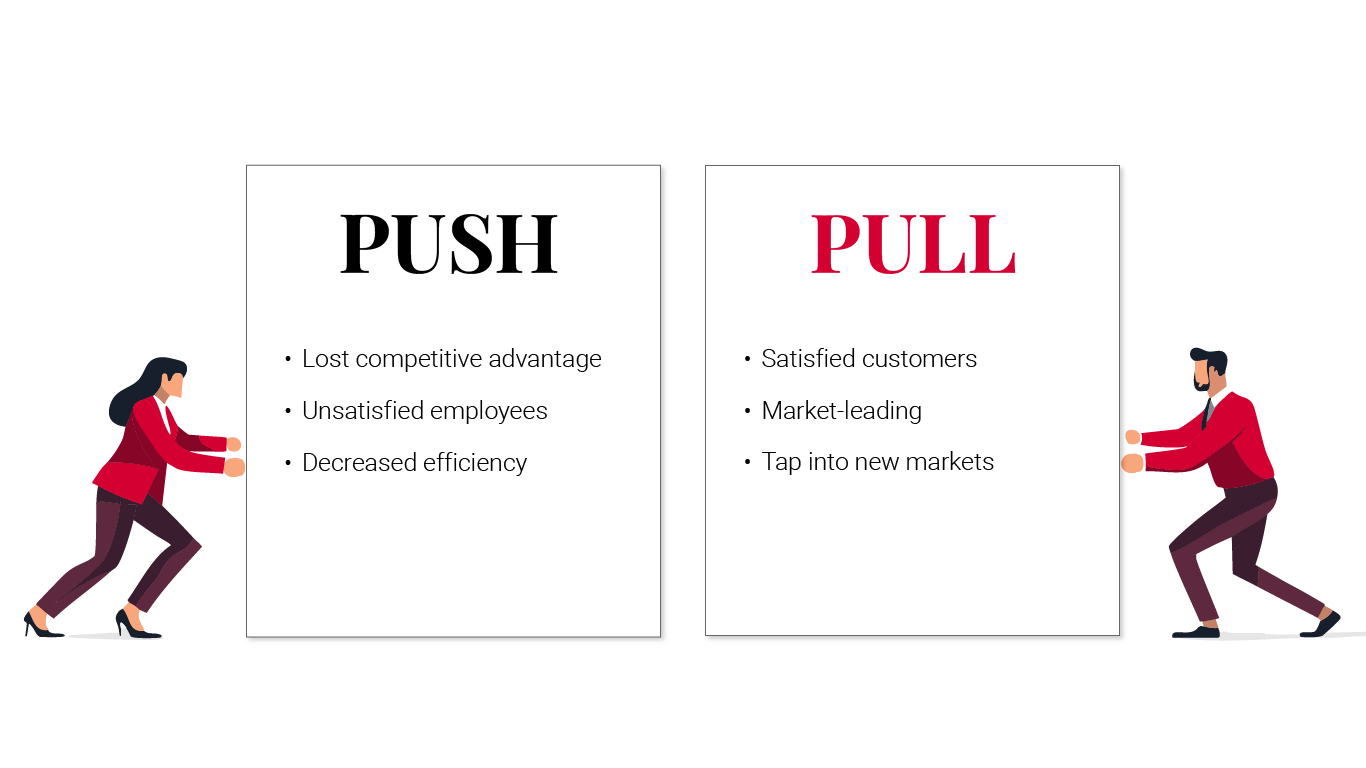
The definition and communication of the change imperative impacting the business is one of the most critical aspects of a change project, and yet often overlooked. I have experienced numerous instances where team members charged with change implementation do not understand the rationale driving the change activity. When team members do not understand the imperative driving the change, it is difficult to foster ownership and motivate change agents to deliver the change.
Shared Change Purpose
Our Shared Change Purpose is an elevator pitch used to sell the proposed change activity to the broader organisation. Like an elevator pitch, it should be concise, succinct, and directly linked to the Change Imperative driving the change activity, ideally comprising measurable targets and a timeline for completion.
When the Change Imperative is not effectively communicated as a Shared Change Purpose, teams struggle to contextualise the activity and create an urgency around its delivery. If we want to embed and institutionalise change, we need to win the hearts and minds of our colleagues, which at Cambridge MC we achieve through communication and engagement across the stakeholder landscape.
“When people are financially invested, they want a return. When people are emotionally invested, they want to contribute.” Simon Sinek
Cambridge MC will help support the creation of the Shared Change Purpose statement, identifying why things cannot remain the way they are, and guiding your organisation to a vision of the desired future state.
Creating Change Readiness in your Organisation
An organisation readiness assessment is an evaluation undertaken by Cambridge MC to understand the overall preparedness of your organisation to support a change activity. This assessment typically involves a review of the following:
• Leadership
• Strategy
• Governance
• IT systems
• Processes
• Technologies
• Culture
Once an organisation readiness assessment has been completed, the Cambridge MC team will support the development of end-to-end user journeys across the impacted areas, identifying the transformation required to achieve our desired future state.
Change management extends beyond individual projects or initiatives, towards the creation of a culture of change readiness. A business culture that embraces change as a constant and necessary part of the business can adapt more quickly, and therefore effectively, to evolving market conditions.
Stages
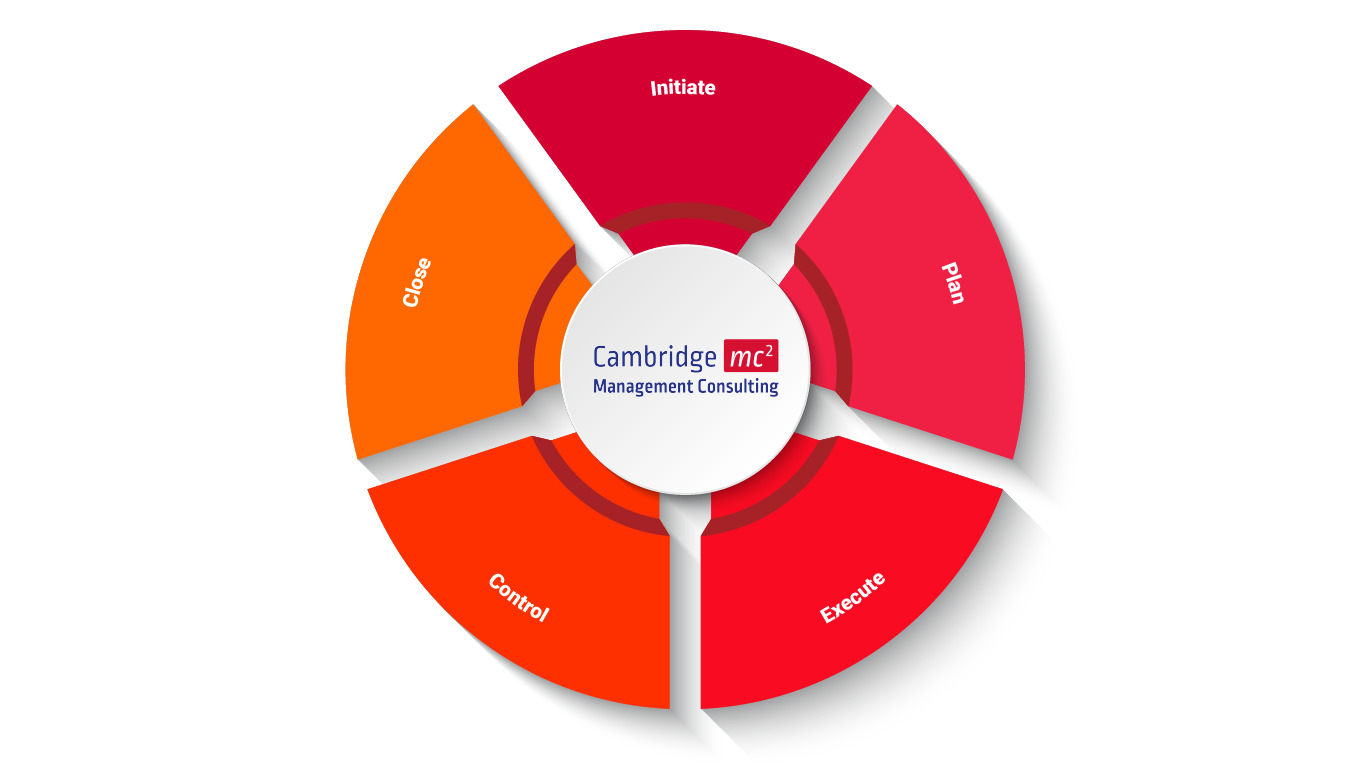
The Cambridge MC Change Management solution provides a rigorous and granular approach to ensure that all projects are delivered to achieve their stated goals.
The Cambridge MC team will support your organisation across the following domains:
1. Planning
2. Initiation
3. Execution (Project Management)
4. Controlling
5. Closing
The Cambridge MC Change Management methodology, provides a robust and repeatable framework to ensure all aspects and impacts of the change initiative across the value chain are considered, providing an effective mechanism to support change value acquisition.
In the following articles in this series, I will explain each stage of our methodology in turn and share the processes we use and the lessons we have learned along the way.
Conclusion
Effective change management ensures that change initiatives align with the organisation’s strategic objectives. In the absence of a structured approach, changes can become disjointed and uncoordinated, leading to inefficiencies and waste. Cambridge MC Change management methodologies help to ensure that all aspects of the organisation – people, processes, technology and governance – are aligned with the desired change, maximising the likelihood of achieving the intended benefits.
By recognising the importance of change management and investing in it as a strategic function, organisations can position themselves to thrive in an environment where change is the only constant.
Ultimately, effective change management is not just about managing change; it's about positioning the organisation for long-term success and sustainability in a rapidly changing world.
If you have any questions, or would like to find out more about our Change Management services, please get in touch using the form below, or email me at: dfitzsimmons@cambridgemc.com
About Cambridge Management Consulting
Cambridge Management Consulting (Cambridge MC) is an international consulting firm that helps companies of all sizes have a better impact on the world. Founded in Cambridge, UK, initially to help the start-up community, Cambridge MC has grown to over 150 consultants working on projects in 20 countries.
Our capabilities focus on supporting the private and public sector with their people, process and digital technology challenges.
For more information visit
www.cambridgemc.com or get in touch below.
Contact - Africa
Subscribe to our Newsletter
Blog Subscribe
SHARE CONTENT











