Our Guide to Achieving the Right Network Solution with SD-WAN and SASE
Q&A: What you need to know about SD-WAN & SASE, with Richard Brown
Richard Brown, former COO of Cambridge MC, chaired a panel at the WAN SUMMIT in London earlier this year.
Here he gives a Q&A about the outlook for SD-WAN at the end of 2021 and farther ahead into 2022. He explains how SD-WAN has moved past the hype and is now developing further in anticipation of the changes brought by 5G.
Richard also discusses how SASE will integrate with SD-WAN to create next-gen security and user experience.
What is SD-WAN and how does it work?
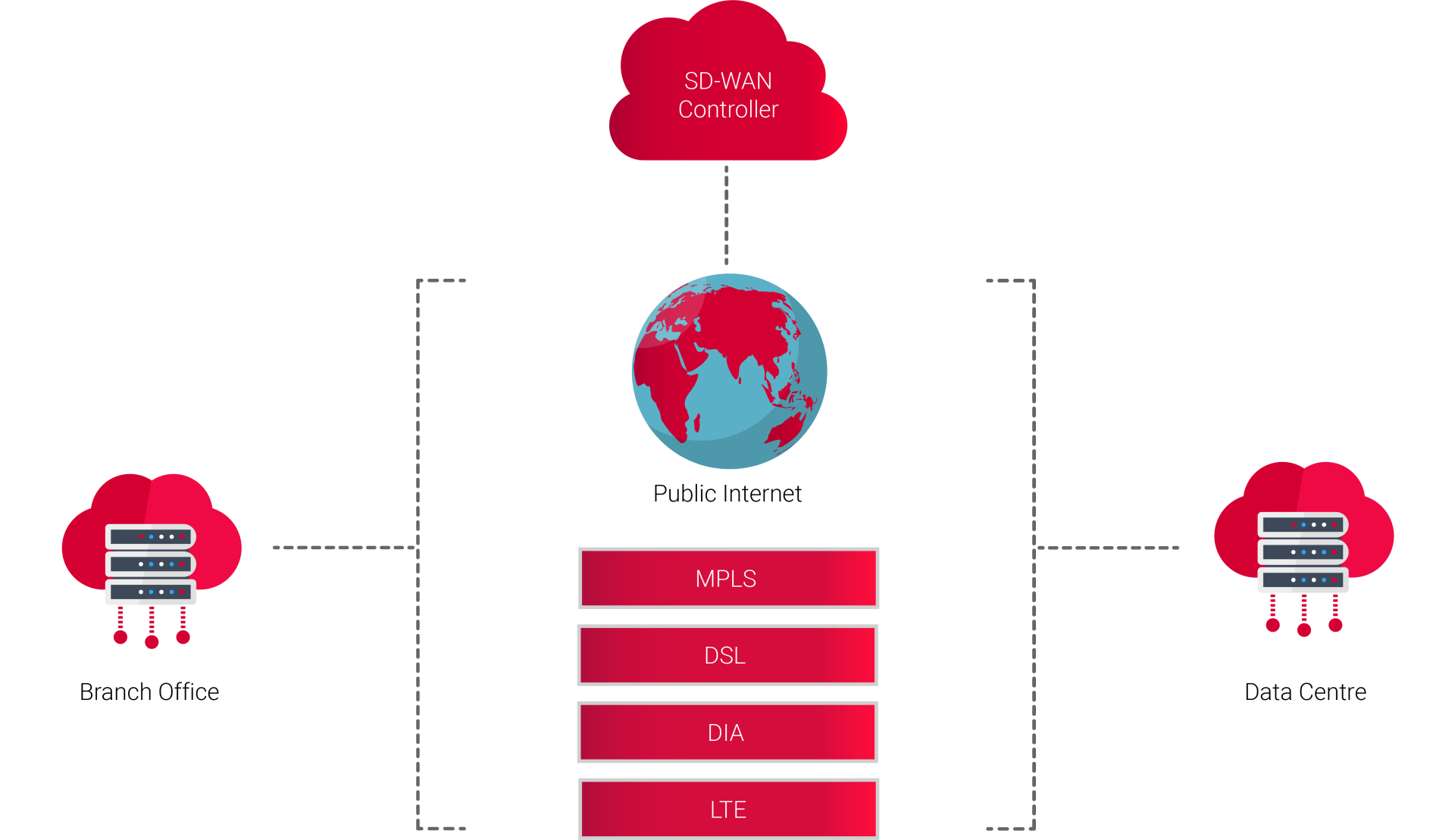
A Software-defined Wide Area Network (SD-WAN) is an overlay technology that allows enterprises to use any combination of transport services, including DIA, LTE, broadband services, as well as MPLS.
SD-WAN simplifies management of a WAN by decoupling the hardware from its control mechanism. This concept is similar to how software-defined networking implements virtual technology to improve data centre management.
Gartner has defined an SD-WAN as having four characteristics:
- The ability to support multiple connection types
- Dynamic path selection, for load sharing and resilience
- A simple interface that can be configured
- The ability to support VPNs, and 3rd party services, such as WAN optimisation controls, firewalls and gateways
SD-WAN is a key enabler to allow enterprises to connect users to applications via an efficient and flexible system, offering increased performance and Quality of Experience (QoE).
What are the benefits of SD-WAN?
SD-WAN uses a centralised control function to direct traffic across the WAN with intelligent programming. This delivers much greater application performance and efficiency, significantly improving Quality of Experience (QoE) for the user. Other benefits include productivity, agility and reduced costs.
Traditional WAN architecture was never designed to support cloud applications and Software-as-a-Service (SaaS). Typically, in scenarios where a router-centric architecture is used with cloud applications, all the data is backhauled to a hub or branch data centre where centralised firewalls provide protection. This can result in poor QoE due to high latency and restricted bandwidth, particularly where expensive MPLS is used as the backhaul.
The SD-WAN model is designed to fully support a hybrid environment, with applications hosted in on-premise data centres, public or private clouds and delivered via SaaS services such as Office 365 and SalesForce, with direct and secure routing of user traffic from their location.
Has SD-WAN moved past the hype phase?
SD-WAN has finally moved through the hype phase. In one recent survey, 50% had either deployed or are in the process of piloting and rolling out SD-WAN.
As recently as three years ago, SD-WAN was being touted as the solution to drastically reduce the cost of the underlay network. The concept was to harness the error correction and load sharing capabilities of the overlay to drive out enterprise grade performance over multiple cheap broadband connections.
It is striking how much understanding and thinking has moved on.
The anticipated move by enterprises away from expensive single vendor MPLS networks and traditional managed router networks is certainly happening. However, the driving factors are often more about keeping up with demand than cost savings.
The reliance on cloud-based services in all areas of business has driven network traffic patterns from traditional hub (data centres) and spoke (users and sites) to user direct to the cloud.
Users need high quality connectivity across the internet to digital applications and public cloud services. And they need ever more bandwidth. The pandemic has also accelerated SD-WAN adoption across most sectors. Despite a high baseline set in 2020, figures show that SD-WAN continued to grow at a stellar rate in 2021.
The move to remote working and the continuation of hybrid working models has created a sustained demand for deployments that provide a fast and stable network for remote collaboration among teams. Vendors are constantly updating their packages; finding new ways to meet the challenges set by IT departments.
What do I need to know about my network underlay?
It’s also become clear that underlay quality is still a factor to be considered. It is simply not enough to say: ‘it’s the internet, what do you expect?’ Internet connectivity must perform consistently to a level that meets business needs.
It’s not enough to solely rely on clever programming within the SD-WAN overlay to overcome bad internet connections. This does help, particularly when you hit temporary patches of poor performance, but nevertheless careful consideration is required to select the internet providers that can deliver the performance you need. With huge growth in streaming, and technology that requires real-time output, networks must also deliver on latency.
Understanding where internet providers peer to other providers to route your user/site traffic to mission critical internet destinations is vital knowledge, particularly internationally. It’s common to find your traffic is actually routing through multiple countries simply because you chose an ISP that did not have peering locally.
What is SASE and does it replace SD-WAN?
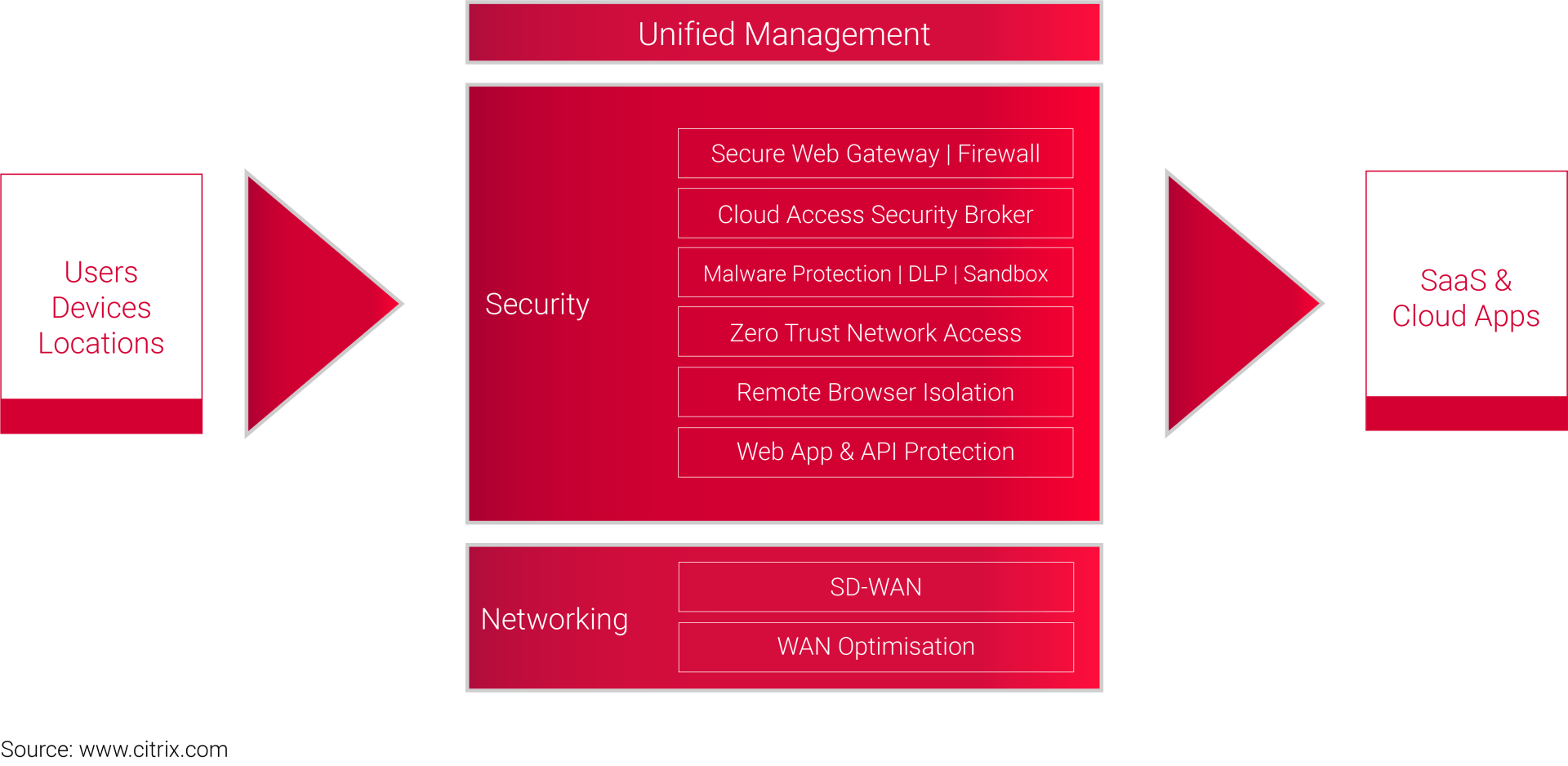
Secure Access Service Edge (SASE) is a security model that was initially proposed in a report by Gartner in August 2019.
Essentially, SASE combines SD-WAN and security services such as CASB (Cloud Access Security Broker), FWaaS (Firewall-as-a-Service) and Zero Trust, delivering them together as a single cloud service.
Security policies enforced on user sessions are tailored to set requirements based on four factors:
- The identity of the connection
- Context – the health and behaviour of the device and sensitivity of the resource being accessed
- Security and compliance policies
- An ongoing assessment of risk in each session
The ‘edge’ part of SASE is usually delivered through PoPs or vendor data centres close to the endpoints —the data centres, users, and devices. In some cases, SASE vendors own the PoPs, while sometimes they use a third-party supplier. The philosophy of SASE is to bring security closer to the user, allowing for authentication and then direct access to resources to reduce latency.
In short, no SASE does not replace SD-WAN. It is more like the peanut butter to SD-WAN's jam.
It is a security extension that will offer many other advantages and help realise the future benefits of 5G and Edge computing. SASE is an evolution of SD-WAN but it does not fundamentally replace or change the infrastructure. It is, at this stage, more a philosophy and a model to improve security protocols in an SD-WAN overlay.
What are the benefits to SASE?
Gartner predicts that 40% of enterprises will have SASE adoption plans by 2024.
Because it is a single service, SASE reduces complexity and cost. Enterprises deal with fewer vendors, and the amount of hardware required in branch locations declines.
IT departments can set policies via cloud-based management platforms, and the protocols are enforced at distributed PoPs close to end-users.
Users have the same access experience regardless of what resources they need and where they are located. SASE simplifies the authentication process by applying appropriate security policies depending on the nature of the resources requested.
SASE also supports zero-trust networking, which bases access on user, device and application, not location and IP address.
Are there disadvantages to SASE?
Unfortunately, getting your underlay right is not as straightforward as we might hope. SASE can also cause performance issues.
You might have great connectivity from an office in Rio de Janeiro to a public cloud service in Sao Paulo over the internet, but if you have to send your traffic to a SASE provider in Miami first, you are unlikely to get the performance you need.
Another disadvantage is a lack of standard or official criteria for SASE. This means some vendors may offer services that do not meet your requirements or the expectations of the model.
We recommend that enterprises take several key things into account:
- Analyse uptime and availability SLAs, along with the breadth of PoPs for connectivity
- Assess network and network security capabilities. SASE platforms do not excel at all network functions and services collectively, so evaluate their strengths and weaknesses. For example, some may excel at SD-WAN and traffic optimization, while others are more focused on CASB or VPN replacement.
There are other issues that are not addressed in the Gartner report. This creates grey areas that will need further research and analysis:
- Scalability
- Latency
- Meeting other requirements: redundancy, reliability, MTTR, customer service
- New metrics for measuring the effectiveness of new parameters in a new environment
- Lack of any official description/standard
How do I choose the right SD-WAN overlay?
SD-WAN overlays are being managed in a variety of ways from internally managed through to buying in a fully managed service. However, as discussed at the WAN summit, ‘vanilla’ managed SD-WAN services are likely to fall short.
In our experience, enterprises were often disenchanted with their traditional managed router service from suppliers, as the race to the bottom on costs often led to suppliers offering only simple ‘up/down’ monitoring of links and fault handing and little more. At the same time enterprise expected a lot more from a ‘managed service’, such as proactive performance monitoring and intervention.
SD-WAN takes both expectations and requirements to a whole new level, because the network is interacting with applications, not just acting as a pipe. While early SD-WAN adopters tended to manage their networks in-house already, and carried on doing so with SD-WAN, others have moved towards a co-managed model where there is a division of responsibility between a supplier with the technical know-how and operational capability to handle faults, and the customer with deeper understanding of their whole ecosystem.
As Network-as-a-Service matures, we will see operators and service integrators that integrate and operate with enterprise clients closely enough to move the boundaries again; so that enterprise takes less of the load.
Research suggests that if enterprises consider existing skillsets, vendors, products and timing of hardware refresh cycles as migration factors, they will reduce their SASE adoption time by half.
AI operations is likely to be the next paradigm. Automation and AI will have a vital part to play in the fast triage of issues and self-heal in the network and is likely to be an important component in bridging the gap between customer expectations of a managed SD-WAN service and affordability.
Despite the investment required to implement SD-WAN and SASE, by both suppliers and enterprise clients, the eventual benefits of improved performance and reduced costs inevitably leads to a convergence between network and security. Remote working and the continuation of hybrid working models has also given SD-WAN a boost
It will be interesting to find out what the cloud giants, AWS, Microsoft and Google, offer as their own SASE recipe to fight off competition. This is an evolving market, and there will be a long list of hybrid models and integrations before the playing field levels out.
The growth of IoT and Edge computing will only increase the need for SaaS applications and cloud storage. To move away from on-premises architecture and security, the SASE model will need greater adoption; this way, end users and devices can gain secure access to all the resources they require with protection from security located close to them. Once users are authenticated, they have direct access to resources, which improves latency.
This convergence will mean enterprises need to consider how they adjust their organisational boundaries to reflect this new reality.
Will SD-WAN help prepare for 5G?

5G will emerge as another important underlay access service to sit under the SD-WAN overlay. Those that have adopted SD-WAN already are likely to find it easier to adopt this access technology that trying to plug 5G into a traditional router network, providing an important and cost effective network access method of particular use cases.
SASE and 5G also offer complimentary benefits —SASE being the best model to create security authentication at the network edge, rather than having direct traffic back to the core. SASE can offer automatic verification and authentication gateways between the user and the enterprise where they are located. It will allow endpoints to access private 5G network slices, authenticating users not only as they cross the enterprise boundary, but also according to rules and hierarchy as they access each specific application.
Early adoption of the SASE model and integrated services, paves the way for a secure 5G network and complete cloud security strategy in the future. With a security and network management platform combined with 5G flexibility and speed (particularly over the last-mile), companies will be prepared for the inevitable confluence of SD-WAN, SASE and 5G.
These future technologies make it an exciting time for SD-WAN. We are past the hype and now well on our way into full adoption. With the advent of SASE, Edge compute and 5G, there will be huge leaps forward for performance, in both bandwidth and latency. AI will also create decision-making at nodes, creating faster and more intelligent network routing.
Find out about our SD-WAN, cloud & network transformation services
Building on decades of experience delivering network change, we have the skillset to deliver the complex network transformation programs necessary to prepare for agile change in rapid markets.
We can transition your network from data centres to the cloud and hosting space such as Azure and AWS. As digital tools and data analytics become increasingly mission-critical, agile networks are required to underpin rapid movement in IT and business strategies. We help you make the right choices among the hype and the myriad options on offer.
Find out more about our SD-WAN and network architecture consultancy services
About Us
Cambridge Management Consulting (Cambridge MC) is an international consulting firm that helps companies of all sizes have a better impact on the world. Founded in Cambridge, UK, initially to help the start-up community, Cambridge MC has grown to over 200 consultants working on projects in 25 countries. Our capabilities focus on supporting the private and public sector with their people, process and digital technology challenges.
What makes Cambridge Management Consulting unique is that it doesn’t employ consultants – only senior executives with real industry or government experience and the skills to advise their clients from a place of true credibility. Our team strives to have a highly positive impact on all the organisations they serve. We are confident there is no business or enterprise that we cannot help transform for the better.
Cambridge Management Consulting has offices or legal entities in Cambridge, London, New York, Paris, Dubai, Singapore and Helsinki, with further expansion planned in future.
Find out more about our
digital transformation services and
full list of capabilities
Subscribe to our Newsletter
Blog Subscribe
SHARE CONTENT