Delivering Digital Transformation, Business Transformation and Legal Compliance
Why Digital Transformation & Business Transformation Must Come Together
Transformation is at the heart of everything we do at Cambridge Management Consulting, and we have always recognised the importance of combining digital transformation (using digital capabilities to modify operations) with business transformation (a significant redesign of your operating model).
70-80% of digital transformation initiatives fail to realise their predicted value. Our experience shows that integrating digital and business transformation is an essential feature of delivering successful transformation and significantly reduces the risks of failure.
Put simply, digital transformation must include business transformation to ensure change initiatives achieve lasting strategic outcomes.
As a consultancy that was founded on principles and lessons learned in decades of complex transformation projects, we strongly emphasise developing a people strategy for your transformation. This is often overlooked, and companies still fail to realise that they pay a high price for focussing exclusively on changing systems and processes.
Consequently, your digital transformation strategy should also include an assessment of the
change readiness of your workforce and its
resilience.
What is Change Readiness and How to Measure it
Change readiness measures how prepared and able your workforce is for a specific change. The results indicate whether you can expect high or low employee resistance, the reasons behind those barriers, and it provides the Board with a reality check on estimated change timelines and expected completion.
Every organisation has unique conditions that can make change management easier or much more challenging. Understanding these attributes will enable your management teams to predict potential obstacles and plan ahead.
A typical assessment includes:
- Culture and value systems
- How much change has already taken place or is taking place
- Leadership styles and power dynamics
- Positive and negative effects of past changes
- Attitudes toward the change initiative
- Workforce resilience

The Importance of Building Workforce Resilience Prior to Business Transformation
Workforce resilience refers to a work environment in which employees can easily adapt to challenging situations, manage stress, and stay motivated. There are a number of indicators that positively influence workforce resilience:
- Early Workforce participation in the change process through established representation guidelines, or in its absence, by proactive company invitation
- Involvement of the workforce in actively developing the change solution
- Early understanding how roles will change and how skills gaps to fulfil the new roles will be addressed by the company
- Early understanding how the company will deal with workforce reductions
To gather information on workforce resilience, we recommend you use an experienced third-party. There are many different methods such as tracking polls and pulse surveys; and increasingly, the use of artificial intelligence (AI) and automated tools that use sentiment analysis.
Depending on the outcome of the above assessments, you may choose to continue or revisit the timing of your business transformation initiatives. If change readiness is found lacking, we can deliver an action plan to help prepare your workforce for the specific changes ahead.
To foster the concept of workforce resilience, you may need to review your values and culture, and provide additional training to management, team leaders and employees.
Providing opportunities for employee feedback and participation in decision-making will help to improve employee experience in your company and an employee desire to contribute to the investment in the company's longer term business success. It cannot be stressed enough that communicating any upcoming change is crucial, as is the need to include employees in your transformation journey.
Start early and offer ongoing training and development opportunities to support employee growth and success throughout digital and business transformation.

Our Unique Focus on People, Processes, and Compliance
Cees Van der Vlugt is a recognised expert in international business transformation, HR and Human Capital Management (HCM). With decades of experience in the Human Resources environment and organisational restructuring, he created our transformation triangle model to deliver digital transformation with the inclusion of business transformation and legal compliance.
This model also includes a strong focus on change readiness, early involvement of the people in your business and stronger governance of a multi-functional consultancy team in delivering a customer centric solution.
The Model was, in its first instance, developed and tested in the German Market, where strong compliance demands are made by Works Councils Legislation. After successful testing in this strict market, it has been expanded to all geographies.
To further complement our service in Germany, we have engaged a legal partner, Pusch Wahlig Workplace Law (PWWL). PWWL is part of a global network of law firms and they support our clients by making sure business changes are implemented with the right level of legal transformation and compliance, with a focus on delivering a customer centric solution with the Transformation Triangle Team.
Dr Tobias Brors, Pusch Wahlig Workplace Law, says "what I like about the partnership between Pusch Wahlig and Cambridge Management Consulting is the solution orientation and customer-centric approach that both companies embrace in their engagement with clients"
How Our Model Addresses the Failure Rate of Digital Transformation
Cees has first-hand experience of the many challenges that come with digital transformation. His business experience has taught him that companies will, without doubt, face an uphill struggle to turnaround their digital capability if the delivery strategy does not include people (Human Capital) from the beginning of the transformation journey.
Furthermore, it is not only early involvement, but also a lack of understanding of change readiness levels in your workforce that can bring digital transformation to a grinding halt. Whether it is the resilience of your workforce, or the efficiency of your processes and procedures, every part of your operating model must be ready to sustain the impact of digital change.
An operating model that fully aligns with the anticipated digital change in your company is often an undervalued element in the process. Without full alignment between proposed digital transformation and operating models, your organisational capability can only reflect the past and present, but not the future.
When these shortfalls are compounded by (legacy) localised process design, lack of communication, and weak training strategies, you will start to see diminishing results and growing resistance from your workforce. The longer this continues, the less chance you have of realising the strategic advantages of your transformation.
The Triangle of Transformation Model
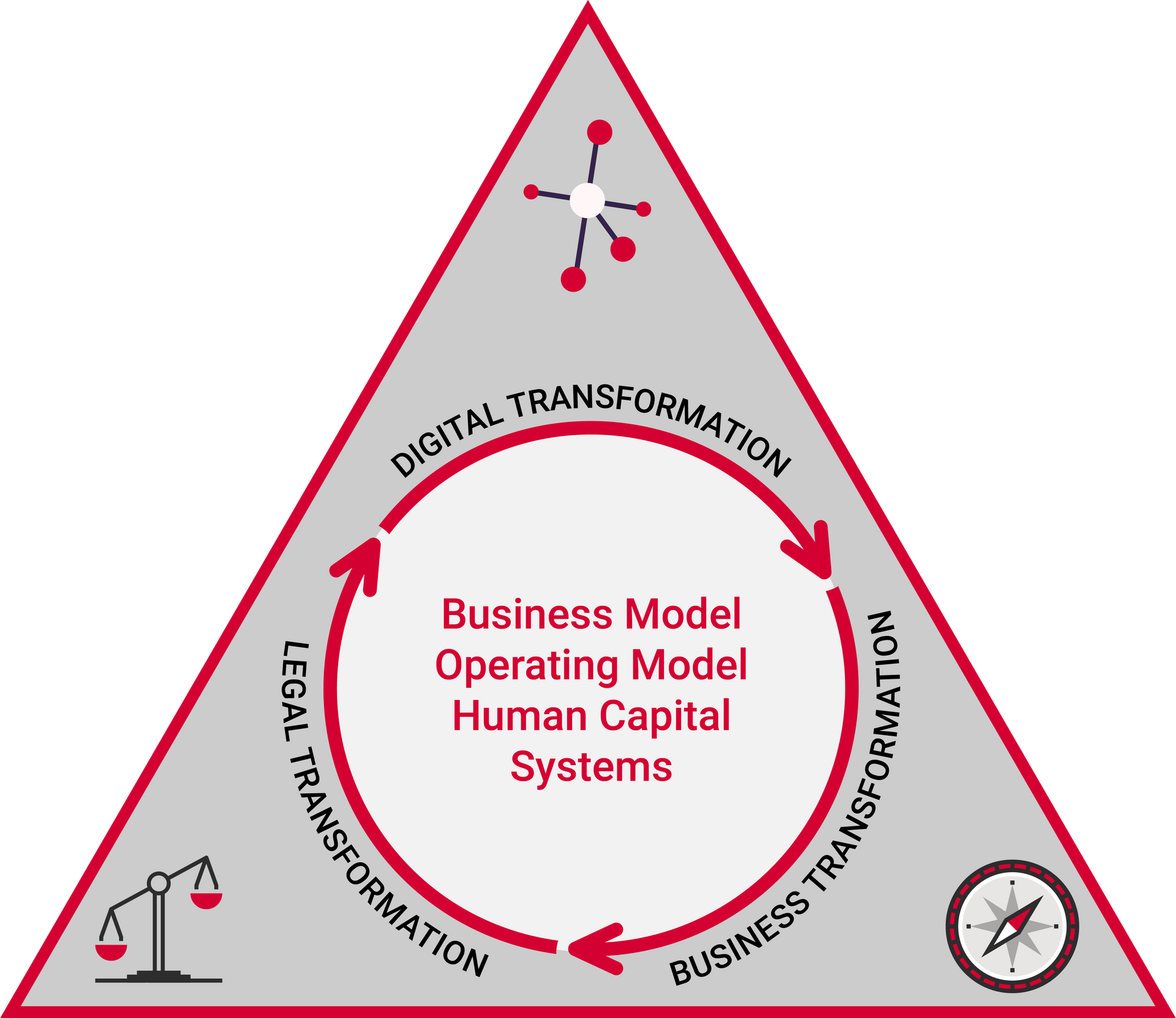
Cees has created a digital and business transformation service that is based on a pre-defined partnership between the providers of digital transformation, business transformation and legal transformation. The emphasis is on driving a customer centric solution through an agreed multi-functional approach, reducing the impact of siloed expertise and substandard solutions.
Multi-functional disciplines are fully aligned with our planning, design, consultancy and implementation services and we work through creating a Transformation Triangle of essential resources that drive a customer-centric, lasting, and efficient change.
There are many reasons why we believe this blended approach is essential to produce the best results.
By combining multi–discipline external expertise into a customer-centric orientated team we reduce the complexity of fragmented support and we can increase our focus on delivering the transformation rather than being pulled into the bureaucracy that surrounds fragmented partnerships.
Yet that is not the only unique strategy employed by our model. As discussed earlier, one common cause of failure during digital transformation is not having a strategy for the people side of your business and not starting early enough.
Our approach continuously balances the employee and business interests. Having an employer and employee representation approach that abstains from technical rationality promotes a sustainable transformation journey.
According to Dr Tobias Brors, Pusch Wahlig, "the development of the Cambridge Management Consulting Transformation Triangle would be a great step in the direction of more effective engagements with Works Councils and the approach could certainly lead to benefits for both employers and Works Councils."
How the German Market Created Our Unique Scalable Model
Cees believes that a model for the German market delivers a scalable solution for international clients. Germany operates a complex set of legislation that needs to be adhered to before making changes to IT infrastructure; and it is specific about the decision-making powers given to German Works Councils, particularly when changes to IT infrastructure affect employees and existing operating models.
This makes it the perfect place to build a scalable model: “A developed business transformation solution for Germany, with its complex employee relations environment, gives us the model from which we can adapt business transformation solutions for other countries with more lenient institutional employee representation.”
Our Legal Partnership with Pusch Wahlig Workplace Law (PWWL)
For legal expertise and legal integrity in the German Market we engaged Pusch Wahlig Workplace Law (PWWL). In collaboration with PWWL, we focus on driving effective labour law solutions, while balancing the customer’s desired digital transformation aspirations and the interests of institutional employee representation.
In the Triangle approach, PWWL provides the vital legal support to implement digital transformation solutions. PWWL is a great example of the kind of law firm that matches our ambitions. The firm is innovative and at the forefront of developments and trends in the field of workplace law in Germany, and strongly connected with digital and business transformation.
PWWL is a leading German employment and labour law firm, with more than 60 highly qualified labour and employment law specialists. Three-time winner of Employment Law Firm of the Year in Germany, they offer clear, concise, goal-oriented solutions in the highly regulated realm of German labour and employment law. With a focus on communicative working relationships, they are a firm driven by proactive strategies which produce results.
PWWL is a member of L&E Global, an alliance of employers’ counsel worldwide. Through our PWWL partnership we also have access to this Global Law Firm Network. L&E is the worldwide leader for cross-border labour and employment law services. Spanning 6 continents, L&E Global member firms are ideally situated to provide clients with the pragmatic, commercial advice necessary to achieve their objectives, wherever they operate.
We feel proud to showcase and be supported by the amazing people that we work with. Digital transformation is full of exciting possibilities and our cutting-edge model and legal support can make it happen for you.
To read more about our Business Transformation capability, go to our service page.
To find out more about our combined Digital Transformation, Business Transformation and Legal Services, contact Cees Van der Vlugt for a free consultation.
About Us
Cambridge Management Consulting (Cambridge MC) is an international consulting firm that helps companies of all sizes have a better impact on the world. Founded in Cambridge, UK, initially to help the start-up community, Cambridge MC has grown to over 120 consultants working on projects in 18 countries. Our capabilities focus on supporting the private and public sector with their people, process and digital technology challenges.
What makes Cambridge Management Consulting unique is that it doesn’t employ consultants—only senior executives with real industry or government experience and the skills to advise their clients from a place of true credibility. Our team strives to have a highly positive impact on all the organisations they serve. We are confident there is no business or enterprise that we cannot help transform for the better.
Cambridge Management Consulting has offices or legal entities in Cambridge, London, New York, Paris, Singapore and Helsinki, with further expansion planned in the near future.
Find out more about our people services and full list of capabilities.
Subscribe to our Newsletter
Blog Subscribe
SHARE CONTENT














