Q&A: What you need to know about the PSTN switch-off in 2025
Your phone is at the end of its line
Many people do not know that at the end of 2025 all phone lines in the UK will be switched over to a fully digital network.
This is happening around the world, and Germany, Japan and Sweden are already ahead of us. Estonia and The Netherlands have already turned off their PSTN networks.
This article is intended for the non-technical reader and technical alike and is intended to dispel some of the myths around the switch-off and provide you with advice and reassurance. You may wish to skip those sections that are less relevant to you.
What exactly is the PSTN?
PSTN or Public Switched Phone Network is the foundation of our communications network and it dates back to Victorian times. It is this messy network of copper wires that transmits the data for analogue phones and fax machines to work. The network is still active in around 14 million homes.
Today, Openreach (part of BT) looks after 192 million km of cables, 110,000 green cabinets, and 4.9 million telephone poles and junction boxes. This infrastructure is no longer fit for the digital age, and it is costly to maintain. As a result, and like many other countries, including France, Germany and Japan, the PSTN network is being phased-out.
What is the PSTN switch-off?
BT announced that as of 31 December 2025 traditional phone lines would be switched off, and all data on those lines transferred to digital services. This means the end of the analogue phone.
Businesses and homes will need to make the switch. And it affects far more than just phone lines. It will impact all kinds of essential devices: fax machines, CCTV, security alarms, lift alarms, alarm pendants, EPOS machines, traffic lights, door entry systems and even cash machines.
In March 2021, Taking Care surveyed more than 2000 people and found that 91% were unaware that all phone lines would be digital by the end of 2025. It is therefore very important to spread the word, and Cambridge Management Consulting is taking this on as a personal project.
What is ISDN and how is it affected?
Integrated Service Digital Network, or ISDN, was created in the 90s and was one of the evolutions of the PSTN system. ISDN was an attempt to digitalise the ‘last mile’ of connections. It splits the traditional copper telephone line into multiple digital channels. These channels operate simultaneously on a single line, allowing multiple phones to make and receive calls.
ISDN was invented in the early days of dial-up internet access, when households couldn’t make a phone call and access the internet at the same time. ISDN has a higher bitrate, and also takes 2 seconds to launch a connection. Those of us old enough to remember will recall the painful dial-up connection speed on a basic landline and the screeching racket it made.
It is important to note that many people still use ISDN for internet access in areas where broadband internet isn’t available. Because ISDN uses the same infrastructure as PSTN, it will also be switched-off on 31 December 2025.
A technical list of all those services affected: WLR, ISDN2 and ISDN30, Local Loop Unbundling Shared Metallic Path Facilities (LLUSMPF), Narrowband Line Share and Classic Products. This will consequently affect products such as Asymmetrical Digital Subscriber Lines (ADSL) broadband and Fibre to the Cabinet (FTTC) broadband.
What are the advantages of digital voice services?
The move to digital phone services (known as Voice over Internet Protocol (VoIP)) offers clear benefits such as better quality, simultaneous multiple calls and accessing your landline in other locations. In the future, providers will be able to develop tools to protect customers against scam and nuisance calls.
This new service will go under a variety of names, such as Digital Voice, IP voice or a branded version.
How will digital voice services be connected to my home or business?
If you’re simply migrating to a digital phone line without upgrading to full fibre, then there won’t be any change to the physical infrastructure. Your service will work using the incumbent wiring —it should simply be a case of connecting your phone to your router. Upgrading to full fibre services has more of an impact because fibre optic cables need to be installed into your home.
Openreach has stated that just over half of properties will be connected using existing telegraph poles where a line from the pole is attached to your home. But in other cases, fibre optic cables will be delivered underground and then through an external wall of your property.
How will the switch off impact UK businesses?
The BT 2025 switch-off will impact an estimated 2 million UK businesses currently operating PSTN or ISDN. There is research showing that 42% of SMEs still use analogue lines for data.
While many larger companies have kept their systems up-to-date, many SMEs need to begin planning their switchover. This will particularly affect businesses who rely on phone or fax communications.
There will also be a burden on care homes, hospitals and public services to update alarms, alarm pendants, security systems and CCTV. Local authorities and those in a position of influence should spread the word in their local area and among their networks to ensure both private and public organisations are well-prepared ahead of stop-sell dates. Some older systems will need to be ripped out and replaced.
You can read BT's five-point checklist for UK businesses here: https://business.bt.com/why-choose-bt/insights/digital-transformation/five-steps-to-digital/
What is Stop Sell and the FTTP Priority Exchange Rollout?
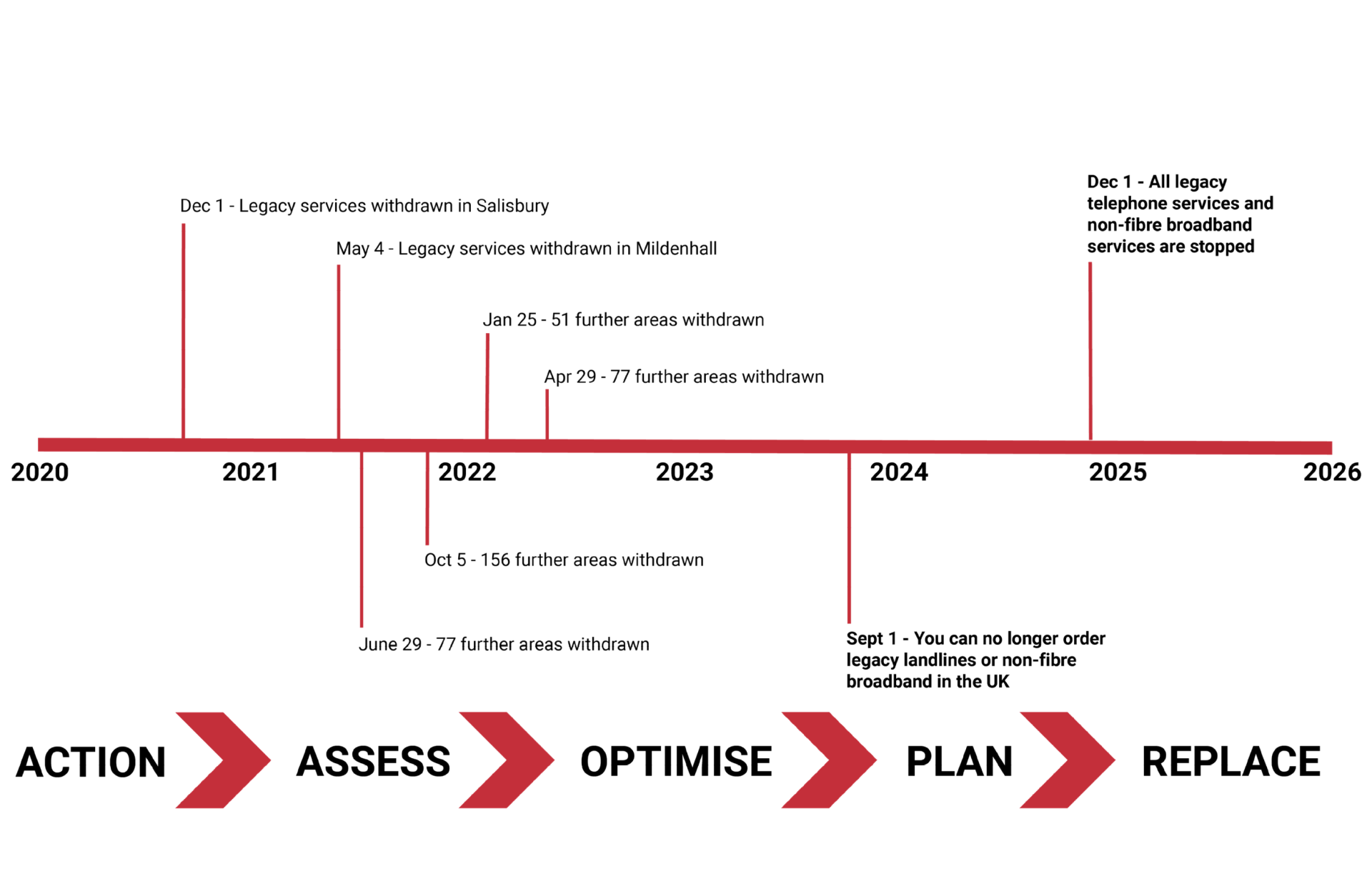
While 2025 might seem a long way off, it is important to know that many services and devices for copper lines will be withdrawn much earlier. By September 2023, you will no longer be able to buy non-digital phones or order non-fibre broadband.
Fibre to the premises (FTTP) is a pure fibre connection from the exchange, into your home or business. The ‘FTTP Priority Exchange Rollout’ allows Openreach to transition to alternative products earlier. When FTTP gets to 75% availability in an area, Openreach will issue a 12-month ‘Stop Sell’ notice. This stops the sale of copper-based products where FTTP is available. When this happens, all new customers, or those switching suppliers, will only be able to buy FTTP. The stop sell has already happened in over 100 locations across the country —with almost 300 exchange areas undergoing stop sell as early as April 2022. Openreach is rolling out its FTTP Priority Exchange program in tranches, with a new tranche being announced every three months.
For a PDF of tranches and stop sell dates from BT Wholesale use this link: https://lnkj.in/t/d6ztq
Timeline
What are the risks of the move to digital voice?
There are a million UK voice-only customers; some of those have no access to broadband. People in this group are more likely to be older and financially vulnerable. They may find the PSTN switch off baffling and hard to grasp.
Ofcom has said that will keep a close eye on the progress made by phone providers to help ensure all customers, particularly those who are vulnerable, are supported through this transition.
If you are reading this article, please make sure older members of your family are aware and prepared closer to the date. There is relatively little public knowledge about the PSTN switch off.
Can the elderly, or those with accessibility needs, still call emergency services during a power cut?
Old landline phones receive power via the line itself and often remain functioning during a power cut digital phones rely on home routers or similar devices.
Ofcom requires phone operators to come up with alternative solutions to ensure customers can still call emergency services. The advice has been in some cases to use a mobile phone, but this is unsatisfactory for vulnerable groups. BT has plans to supply vulnerable customers with a back-up battery that ensures that devices will work for an additional hour if an outage occurs. Virgin Media's stated solution is a device with its own battery that allows landline phones to connect to mobile phone services.
How we can help
If you are an SME, organisation, charity or other body with concerns about the PSTN switch off, please get in touch by email and we will offer advice to get you started.
We can help with your transition, potentially identifying services that are no longer required and saving you money. We can create a digital replacement strategy to ensure continuity of services and transform your current communication capabilities.
To discuss this further, please get in touch with Jeff Owen at jowen@cambridgemc.com
About Us
Cambridge Management Consulting (Cambridge MC) is an international consulting firm that helps companies of all sizes have a better impact on the world. Founded in Cambridge, UK, initially to help the start-up community, Cambridge MC has grown to over 200 consultants working on projects in 25 countries. Our capabilities focus on supporting the private and public sector with their people, process and digital technology challenges.
What makes Cambridge Management Consulting unique is that it doesn’t employ consultants – only senior executives with real industry or government experience and the skills to advise their clients from a place of true credibility. Our team strives to have a highly positive impact on all the organisations they serve. We are confident there is no business or enterprise that we cannot help transform for the better.
Cambridge Management Consulting has offices or legal entities in Cambridge, London, New York, Paris, Dubai, Singapore and Helsinki, with further expansion planned in future.
Find out more about our digital transformation services and full list of capabilities
Subscribe to our Newsletter
Blog Subscribe
SHARE CONTENT










