Should we be Using Predictive Analytics in Digital Infrastructure Development?
The Environmental Trade-off in Digital Infrastructure Development
Digital development presents a double-edged sword. On the one hand, it boosts productivity through remote work, AI, and automation, with the potential to lift billions out of poverty. Yet, at the same time, the rapid growth of infrastructure required to support these developments will need a corresponding growth in decarbonisation to avoid a climate catastrophe.
The German Advisory Council on Global Change highlights this contradiction: “uncontrolled digital change threatens to undermine the important foundations of our democracies” [1].
This article takes an in-depth look at how global institutions push the mantra of ‘digitisation’ as a developmental priority for nations while failing to adequately acknowledge the huge climate impact of this enterprise. This obscuring of consequences eases the way for a rapid extension of infrastructure that consumes billions of gallons of non-renewable resources annually.
In this article, I suggest that detailed modelling and forecasting are one of the major pillars needed to address this dichotomy. I will set out an approach and resources for modelling the digital demand to design a more predictive approach to digital infrastructure builds.
The Environmental Impact of a Data Explosion
The amount of data flowing over global digital infrastructure has exploded 300-fold over the last 10 years [2], with the next 20 years expected to see faster-paced growth on the back of the continued digitisation of life and entertainment, as well as from huge numbers of people in developing countries coming online for the first time.
This explosion is a good thing—the UN’s Sustainable Development Goal (SDG) 9 aims to provide universal and affordable access to the internet by 2030 [3]. Access to the internet and digital services strongly correlates with improvements in education, healthcare and women’s empowerment.
As increasing numbers of people come online, and the scale of their data use grows, a variety of digital infrastructure will need to be built or scaled up if the digital ambitions of countries and trading blocks are to be realised.
Connectivity is one part of the solution—increased coverage of broadband, mobile and satellite will undoubtedly support these targets. But, ultimately, all that data traffic needs a destination point, in the form of data centres, which, unfortunately, require vast sums of power.
In the USA, data centres are expected to consume 380TWh of electricity by 2027 [4], almost 9% of the country’s total consumption. Ireland faces an even larger burden with digital infrastructure expected to consume 33% of the country’s total electricity by 2026 [5], and potentially 70% of the country’s electricity by 2030 [6].
Ireland and the USA have reliable national power grids, but this is not necessarily the case in developing countries. In Nigeria, data centres and mobile towers rely heavily on diesel generators, burning nearly a billion litres of diesel annually. This is a country where the average annual mobile data traffic per subscription is only 6GB per year [7], just over 0.1% of the average traffic from a UK subscriber.
To achieve universal internet access for a population that is estimated to cross the 300 million threshold by 2036 will require an exponential growth in digital infrastructure. If Nigeria remained dependent on diesel generators, and data consumption on a per-person basis reaches the UK’s level of data traffic, then the country would consume 9 trillion litres of diesel a year—over 100 times the amount of diesel consumed by the entire world in 2022 [8].
This single event would create a climate catastrophe—even if the UK, France, Germany, Spain and the Nordics reduced their CO2 emissions to zero, this would offset less than half of this increase. This is of course the worst-case scenario. Grid infrastructure has developed across West Africa and there are a multitude of projects which are building green energy infrastructure. But there has yet to be a major MNO, TowerCo or data centre company which has shown significant year-on-year reductions in emissions.
It is unjust to expect developing nations to slow down or halt their digitisation while developed countries reap the benefits of a digitised economy. Instead, alternative approaches to managing global emissions are needed. And this is where predictive analytics become a crucial tool for forecasting future demand. These tools and models will support the development of alternative strategies for power generation and implement methods to reduce emissions from digital infrastructure.
A predictive tool that models national network traffic growth and compares it to projected digital infrastructure expansion will help identify underserved areas early, enabling better planning of digital and power infrastructure. Early planning allows for the integration of renewable energy, natural cooling solutions, and partnerships with sustainability experts to reduce emissions.
Creating the Model: Traffic vs Digital Infrastructure
To address these challenges, David Jones, an Associate of Cambridge Management Consulting, has developed a comprehensive model that examines global internet traffic on a country-by-country basis and compares it to existing and planned digital infrastructure within those countries.
This model considers several factors:
- Population Growth: Increasing numbers of internet users
- Economic Growth: Rising wealth levels leading to more internet usage
- Internet Penetration: A growing proportion of each country’s population getting online
- Usage Patterns: Moving towards video transmission over the internet significantly increasing traffic
- B2B and M2M Traffic: Business-to-business and machine-to-machine Internet traffic growth
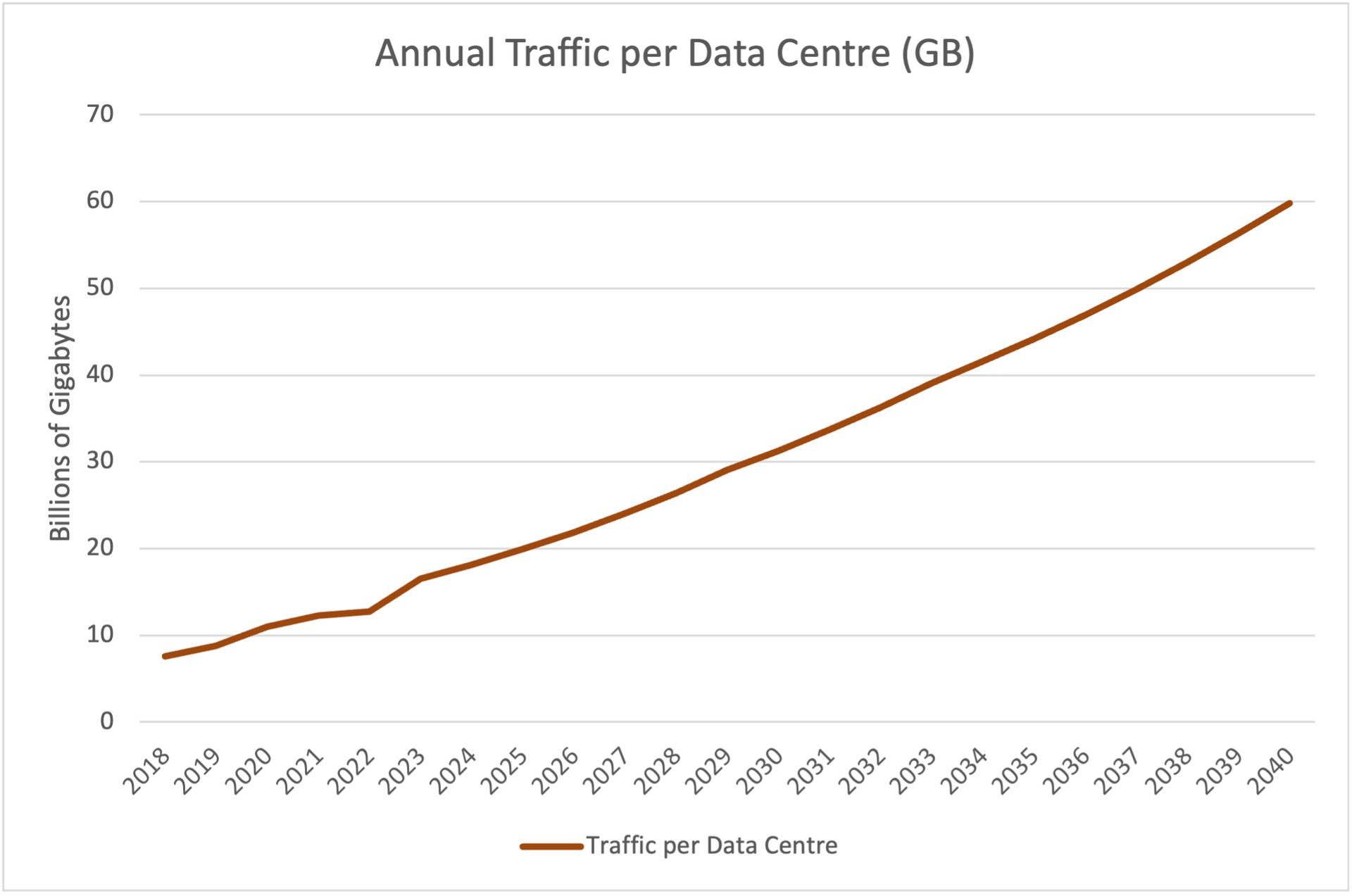
This model projects internet traffic growth over the next 20 years, if data traffic growth follows a logarithmic curve, increasing at a decreasing rate. In Germany and other developed nations, the rate of traffic growth slows once it reaches a certain threshold, as there is a natural limit to how much HD video a person can consume. By comparing these projections with a database of over 10,000 data centres, including locations and power consumption, it is possible to identify regions with underdeveloped or overdeveloped digital infrastructure.
Note: This model does not account for the growth in generative AI, which adds further demand on a strained digital infrastructure. For more information on this subject, see our recent article: Building an AI-ready infrastructure.
Initial Results
When we run this model and compare countries, what immediately becomes clear is the difference in scale between the growth of digital infrastructure and internet traffic. Ireland’s digital infrastructure is increasing at a rate faster than its internet traffic, while in countries like Bangladesh and Algeria internet usage is growing ten times faster than the digital infrastructure that supports it.
David has modelled 76 countries and will be completing another 50 over the next few months. So far, the CAGR of internet traffic is around 30%, and the CAGR of data centres is around 12%.
What’s clear from this graph is how the difference in growth rates compounds over time, and that as the years progress the gap between traffic and infrastructure widens. This shows that over time the availability of infrastructure will become a massive limiting factor to digital experience. Eventually, the lack of adequate infrastructure may even prevent citizens from accessing essential internet services.

Country Spotlight: Kazakhstan
The early modelling highlights several of the usual suspects in terms of investment in digital infrastructure. Turkey, Saudi Arabia and China all feature highly on the ranking of locations where internet traffic outpaces digital infrastructure.
Kazakhstan is often not included in this categorisation—however, as shown by the diagram below, it should be given far greater consideration.
In the next ten years, the mobile data consumed by the average Kazakh will grow by 600% from 200GB to 1200GB, with fixed data increasing 400%. This is against a backdrop of limited investment in their data centre capacity.
There are many factors to analyse when looking at digital infrastructure including power availability, ease of doing business, international connectivity, borrowing costs and macro-economic forecasts. This analysis indicates that there will be a growing unmet demand for digital infrastructure in Kazakhstan. By starting the planning process now, we can use more environmentally friendly methods to power and cool data centres, instead of waiting until the demand becomes critical and building data centres becomes reliant on fossil fuels.
The Trade-off: Speed vs Sustainability
At its core, the process of finding, designing and building a data centre is intensely time-consuming. A single-tenant data centre takes on average 18 months to go through planning, engineering, construction and commissioning phases [9]. Given a significant increase in demand, this puts many data centre projects under intense time pressure.
These time constraints lead to organisations making decisions that prioritise speed of completion over emissions generation. Using diesel generators for power, buying existing buildings and retrofitting them and location selection are all decisions made to prioritise the speed of completion.
This time pressure limits the ability of design teams to engage with alternative strategies for power reduction and the maximisation of renewable resources. This is not to say that firms don’t consider energy and environmental impacts, but they are usually a low priority.
Some of the key trade-offs surround building design: old, retrofitted buildings aren’t usually designed to maximise airflow and are harder to modify to increase ventilation. They are also unlikely to maximise the cooling benefits that occur from subterraneous data centres, with a recent study estimating that this could result in a 60% reduction in power consumption. Tesla’s new gigafactory highlights advantages of advanced planning. The company claims that the use of liquid cooling has achieved an 89% reduction in energy consumption at their 130MW data centre. [10]
A Predictive Approach to Design
David’s model also predicts other factors that can inform the approach to design and planning:
- Unmet demand in digital infrastructure capacity
- Turning points when a nation’s digital infrastructure becomes unviable for the traffic it needs to support
- Opportunity spaces for additional infrastructure development
Predictive demand modelling enables advanced planning because it provides more time to design the best solutions for future needs. This approach can reduce data centre power consumption by up to 90% through optimised design and strategic resource allocation.
By forecasting future internet traffic and infrastructure requirements, companies can strategically find data centres near renewable energy sources, cutting reliance on fossil fuels. Integrating energy-efficient technologies, such as advanced cooling systems and high-efficiency hardware from the outset, ensures lower electricity usage throughout the data centres’ lifecycle.
Additionally, advanced planning enables data centres to play a crucial role in reducing community emissions. By implementing innovative solutions like those used by Deep Green data centres (see our press release about our partnership with Deep Green), waste heat generated by servers can be repurposed to provide heating for nearby communities. This reduces the carbon footprint and provides sustainable heating, providing the use case for a symbiotic relationship between digital infrastructure and environmental stewardship.
The Next Stage of our Model
We are about to cross a Rubicon, and it is essential that the connection between digital infrastructure and emissions permeates into the global consciousness. This will be necessary for the kind of public pressure required to move governments on these issues.
Cambridge Management Consulting is focused on improving the quality of decisions that infrastructure firms make, finding unmet opportunity spaces and working with organisations to make key infrastructure decisions.
As David evolves his model to include local power availability, subsea cable offload points, ease of doing business scores and real estate costs, the level of granularity will increase, and we will bring the model to bear at a city-level as well as a country level.
Along with this, we will work with digital infrastructure companies, investment vehicles, telecommunications firms and power companies to embed modelling solutions to their infrastructure planning.
Cambridge Management Consulting
Cambridge Management Consulting (Cambridge MC) is an international consulting firm that helps companies of all sizes have a better impact on the world. Founded in Cambridge, UK, initially to help the start-up community, Cambridge MC has grown to over 160 consultants working on projects in 22 countries. Our capabilities focus on supporting the private and public sector with their people, process and digital technology challenges.
What makes Cambridge Management Consulting unique is that it doesn’t employ consultants—only senior executives with real industry or government experience and the skills to advise their clients from a place of true credibility. Our team strives to have a highly positive impact on all the organisations they serve. We are confident there is no business or enterprise that we cannot help transform for the better.
Cambridge Management Consulting has offices or legal entities in Cambridge, London, New York, Paris, Dubai, Tel Aviv, Singapore and Helsinki, with further expansion planned in future.
If anyone is interested in using David's model or has further questions, please reach out at djones@cambridgemc.com or use the contact form below.
Find out more about our data centre services.
Find out more about our
sustainability services.
Footnotes
[1]
https://issuu.com/wbgu/docs/wbgu_fs1-2019_en?fr=sODZiZTM4MDU3Mg
[2]
https://www.ericsson.com/en/reports-and-papers/mobility-report/dataforecasts/mobile-traffic-forecast?gad_source=1&gclid=CjwKCAjwvvmzBhA2EiwAtHVrbypuKnOSS1k1w2hFZ6FmRjDmU0pj08f1mD4ENPkn7_ytu4s2fvcO5RoCFYQQAvD_BwE&gclsrc=aw.ds
[3]
https://www.un.org/techenvoy/content/global-connectivity
[4]
https://www.aresmgmt.com/sites/default/files/2024-06/Digital-Convergence-Green-Paper_June-2024.pdf
[5]
https://dcnnmagazine.com/data-centres/data-centres-in-ireland-to-consume-one-third-of-electricity-by-2026-schneider-electric-responds/
[6]
https://www.irishtimes.com/news/politics/data-centres-could-use-70-of-ireland-s-electricity-by-2030-committee-to-hear-1.4685589
[7]
https://www.itu.int/en/ITU-D/Statistics/Dashboards/Pages/Digital-Development.aspx
[8]
https://www.procurementresource.com/blog/industrialisation-and-growth-in-population-is-driving-the-global-diesel-market
[9]
https://www.juniper.net/us/en/forms/2024/top-5-data-center-trends-for-2024.html?utm_medium=sem&utm_source=google&utm_campaign=EMEA_ALL_Stein_Paid_Media&utm_content=Misc_d_emea_uk_asdc_nonbranded_crdc_en&utm_term=building%20your%20own%20data%20centerpc_696026707333&utm_gclid=CjwKCAjwnK60BhA9EiwAmpHZw3fmFXA32neb9LHKzIURuHV1AXgJAA-5cUlrtnA3CDndZDR1a1dXFxoCLzgQAvD_BwE&gad_source=1&gclid=CjwKCAjwnK60BhA9EiwAmpHZw3fmFXA32neb9LHKzIURuHV1AXgJAA-5cUlrtnA3CDndZDR1a1dXFxoCLzgQAvD_BwE
[10]
https://www.tomshardware.com/tech-industry/artificial-intelligence/elon-musks-liquid-cooled-gigafactory-data-centers-get-a-plug-from-supermicro-ceo-tesla-and-xais-new-supercomputers-will-have-350000-nvidia-gpus-both-will-be-online-within-months
Contact - NIS2 Article
Subscribe to our Newsletter
Blog Subscribe
SHARE CONTENT