PSTN Switch-Off Delayed to 2027: What this means for You
UPDATED: February 2025
In this article we look at the extension to the PSTN Switch-Off date and explain why it is happening. We consider why businesses and local authorities should not delay in their PSTN migration plans. Then we look at three UK sectors—the Public Sector, SMEs & Large Enterprises, and Property & Real Estate—and assess the challenges they face and what they can do to avoid costly pitfalls.
What is the PSTN Switch Off?
The Public Switched Telephone Network (PSTN) is the traditional analogue network in the UK that uses copper cables to carry landline voice calls between users. It has been the backbone of the UK's telephony network since Victorian times. The PSTN is an aging network that is becoming harder and more expensive to maintain. It is not capable of handling the speeds and data volumes demanded by modern telecommunications
By the end of January 2027, BT and Openreach, along with other phone companies, plan to decommission the Public Switched Telephone Network (PSTN). This transition marks a shift towards digital services, such as Voice over Internet Protocol (VoIP), which will replace traditional landline services.
The PSTN supports over 300 recognised use cases, including alarm systems, medical devices, and monitoring equipment. The implications of this transition will be far-reaching, affecting residents, businesses, public services and all industries in the UK.
Please note: This article is written for a range of audience familiarity. Discussion of the PSTN switch off often uses some technical language—please see the Appendix below for a glossary of terms.
When is the New Date?
BT has recently announced an extension to the Public Switched Telephone Network (PSTN) switch-off in the UK. The previous deadline of December 2025 has been postponed to 31 January 2027.
Openreach (a subsidiary of BT) has reacted to this announcement by extending the withdrawal timeline of their Wholesale Line Rental family of products (landline and ISDN services) to the same date.
Why is the PSTN Switch-Off being Postponed?
This delay is primarily due to the difficulties in securing the smooth transfer of vulnerable customers, such as the complex migration issues that could disrupt continuity for safety-critical devices, such as telecare devices, including personal alarms, which in some cases were found to stop working during the initial stages of the switch-off. It is estimated that 2.3 million people in the UK currently use personal alarms that rely on the telecommunications network.
Act Now before Time & Resources Run Out
It is wrong to think that the extra 13 months given by the delay means pushing back your plans for action. We highly recommend that you continue to focus on December 2025 in order to achieve risk free migrations that ensure continuity of services from the simple to the complex. BT recently made the same recommendation, urging its business customers to act before the end of 2025.
The transition to digital alternatives could take at least 6-9 months, with additional time needed for testing and a break-fix approach to solutions. A critical first step for all businesses is to comprehensively audit all your phone lines and identify systems that rely on the PSTN.
Transitioning early is critical for the public sector and other organisations that provide a duty of care to vulnerable people and the elderly. We look at those responsibilities in more detail below.
We also make a case for urgent action by property owners and building operators—to address service continuity, fire safety and security issues.
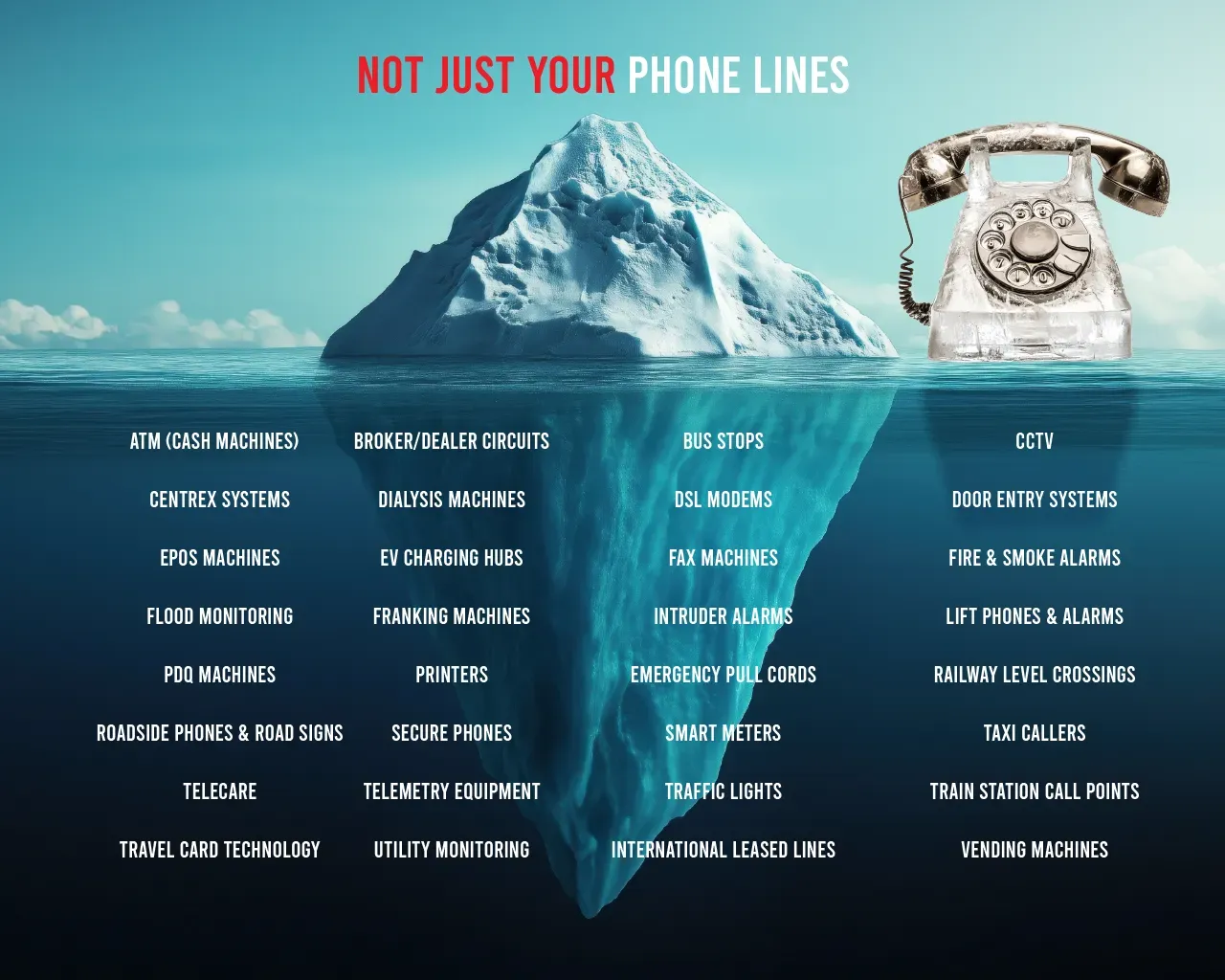
List of Affected Equipment
Many businesses still rely on PSTN service-based technologies and will be severely impacted by the switch-off. We have provided a quick reminder of affected services other than your landline below to help with general awareness (please note, this is not an exhaustive list, and you should contact your Communication Provider (CP) and conduct a thorough review of your equipment and PSTN lines):
- Air Con Units
- ATM (cash machines)
- Broadband services using ADSL or FTTC
- Broker/Dealer circuits (see also: Secure Phones)
- Bus Stops
- Cardiac Arrest phones
- Car Parks (including lifts, CCTV and alarms)
- CCTV
- Centrex telephone systems
- Dial-Up and DSL Modems
- Dialysis Machines
- Door Entry systems (and similar systems running on ISDN)
- Electronic Points of Sale (EPOS)
- EV Charging Hubs
- External Bells
- Fax
- Fire & Smoke Alarms
- Flood Monitoring
- Franking Machines
- Hazardous Environment Phones
- Intruder Alarms
- Lift Emergency Lines/Alarms
- Medical Equipment
- PDQ Machines
- Printers
- Emergency Pull Cords
- Railway Level Crossings
- Redcare (a security monitoring service provided by BT)
- Roadside Telephones
- Road Signs
- School Security
- Secure Phones (Brent phones)
- Shop 3rd party terminals
- Smart Meters
- Telecare (and other healthcare monitors)
- Telemetry equipment (data loggers, remote sensors etc.)
- Traffic Lights
- Train Station Call Points
- Travel Card technology
- Utility Monitoring
- Vending Machines
How the PSTN Switch-Off Impacts Different UK Sectors: What You Need to Do
We will now look at how the PSTN Switch-Off will impact the Public Sector, SMEs & Large Enterprises and Property and Real Estate.
Public Sector
Given the lack of a national plan or central funding for the necessary infrastructure upgrades, responsibilities for welfare and safety will impact at a local level on councils, healthcare services, social housing, fire departments and third sector organisations (charities and community groups). If these upgrades do not get funded and planned in detail (and if alternative digital solutions are not adequately tested under real scenarios) then emergency services could fail at a critical moment, putting vulnerable people at risk.
Key areas impacted by the PSTN switch off that are acutely relevant to Local Authorities (LAs) are as follows:
- Telecare devices
- Fire and security alarms
- Specialist housing and care homes
To help public bodies plan and budget their migration strategy, we have grouped the major responsibilities into five areas:
1. Funding & Planning
Councils will need to work with hospitals, schools and other public bodies, alongside Communication Providers (CPs), to share resources, overcome common problems, and model future costs. Councils can also help to secure funding from government schemes and may be able to provide other means of financial support to help local bodies.
2. Protecting the Vulnerable
Ofcom has ruled the following: ‘If you are dependent on your landline phone – for example, if you don’t have a mobile phone or don’t have mobile signal at your home – your provider must offer you a solution to make sure you can contact the emergency services when a power cut occurs. For example, a mobile phone (if you have signal), or a battery back-up unit for your landline phone. This solution should be provided free of charge to people who are dependent on their landline.’
Councils should continue to work with CPs to provide these services free-of-charge as well as providing a smooth transition and clear communication for vulnerable people.
3. Continuity of Public Services
Understand how the PSTN supports the services offered in the local community, for example: emergency lift lines in council buildings, payment machines in cafes, and local call centres/help desks. Involve all impacted departments as this minimises blind spots and facilitates the sharing of best practices. Affected departments include adult social care, highways, flooding, estate management, and risk management. View the migration as a Business Continuity challenge as this has already helped some LAs to galvanise local parties. The Government has set up a Working Group for the digital switchover to share information: https://www.local.gov.uk/our-support/cyber-digital-and-technology/digital-switchover/working-group
4. Digital Inclusion
Ensuring adequate internet infrastructure is a key responsibility of local councils. They need to work with Communication Providers (CPs) to address digital exclusion in their jurisdictions, particularly in rural and underserved areas, to support new IP-based communication systems. Wireless-based solutions, such as 5G, IoT, or LORaWAN, and low orbit Satellite communications will also offer an option for the hardest to reach locations.
5. Awareness
Unlike the shift to digital TV, which was government-initiated, the phase-out of the PSTN is industry-driven because the network is privately owned. Consequently, it is unlikely there will be a government-sponsored national campaign to spread awareness of these changes and the risks involved. It therefore falls to local authorities, in conjunction with CPs and local groups, to try and disseminate this information to their communities, and in particular to vulnerable people.
Of particular importance is the response to telecare devices in supported housing and care homes run by Local Authorities (LAs) or third-sector organisations.
Telecare National Action Plan
At the end of 2024, Telecoms Minister Chris Bryant convened a roundtable in London with telecoms companies to address concerns surrounding the digital switchover and its impact on telecare users. The meeting, which included representatives from BT, Virgin Media, Vodafone, and Sky Broadband, focused on safeguarding vulnerable telecare users during the upgrade from analogue phone lines to digital networks.
Key outcomes from the roundtable included:
- Telecare National Action Plan: Bryant agreed to a new 'Telecare National Action Plan' with major UK broadband and phone providers. This plan, slated for publication before the end of 2024, is designed to offer more protection to vulnerable telecare users as phone lines are upgraded to digital (IP-based) networks.
- Checklist of Safeguards: Telecoms companies were directed to complete a strict checklist of safeguards before transferring customers from analogue to digital phone lines.
- Engineer Visits: Companies will be required to offer engineer visits to vulnerable customers. These engineers will personally test the telecare alarms to ensure they continue to function after the household transitions to the digital network.
- Battery Backup Solutions: Bryant urged companies to extend the power of battery back-up solutions beyond the existing one-hour minimum. This is aimed at maximizing resilience and ensuring access to emergency services during power outages
How we can Help
Our Public Sector team can help local councils and other public bodies by providing strategy, financial planning, procurement and project management services as and when you need them. Get in touch with Craig Cheney, Managing Partner and lead for Public Sector & Education, to discuss a range of services which might suit your needs: ccheney@cambridgemc.com.
View our Public Sector & Education services.
SMEs & Large Enterprises
Surveys indicate that around 9 out of 10 UK businesses have essential services that rely on the PSTN. Your business needs to prepare for the 2027 switch-off by transferring your tradition phone line, and any device that uses it, to a digital alternative.
While communication providers (CPs) are aware of which organisations are using PSTN services and should contact them directly, the overall responsibility for upgrade and hardware updates falls to the customer. Many businesses potentially require new phone handsets and may need to retrain staff on new service dashboards.
Larger businesses should conduct a thorough analysis of the potential impact and identify outdated equipment to replace. This is also an opportunity to leverage the benefits of IP by incorporating call analytics and other AI or cloud-based tools. We highly recommend you start now to prevent a costly and stressful transition or worse, a last-minute overhaul that creates service disruption.
You may wish to enlist a third-party solution provider who will migrate all of your phones numbers to IP-services, provide phones and headsets and a call management platform. This could reduce the headache for your business and prevent the risk of downtime and outages when you switch.
How we can Help
To find out more about how our services and experts can help your business, contact Phil Laws, Senior Partner - PSTN Services, and his team: plaws@cambridgemc.com.
If you operate a call centre and need help with the migration of services and/or setting up a call management platform with AI analytics, get in touch with our Contact Centre specialists, Simon Kissane and Marcel Biesmans: skissane@cambridgemc.com. We have partnered with Dialpad, an industry-leading AI-powered Customer Intelligence Platform.
Property & Real Estate
Many buildings rely on PSTN lines for critical services such as lift emergency calls, fire alarms, security systems, door entry, monitoring, and management systems. Once the PSTN service is decommissioned, these services will cease to function without warning, leading to potential safety compliance risks.
Both owners and operators in the property sector need to act now. You should start planning upgrades and the migration of your infrastructure to digital voice services using a systematic methodology. If you lack the in-house experience or this is a drain on internal resources, consider using a third party to conduct a comprehensive review of your IT and telephony equipment to create a detailed migration and upgrade strategy.
Companies and organisations potentially affected by the PSTN switch-off include: retailers; department stores; shopping centres; outlet centres; retail parks; entertainment and leisure venues; distribution and logistics centres; service stations; drive-thru facilities; office buildings and campuses; factories; advanced manufacturing facilities; hospitals; health centres; care homes; schools; universities; sports facilities and many more.
This is a complicated process with many project streams for those businesses and organisations that have a property portfolio/estate to manage. Public Sector organisations that service and maintain various distinct property types, such as social housing, will also face significant challenges.
It may be in your best interest to upgrade these services under one programme, using a central PMO and procurement process, and a single solution provider, to ensure targets are met on time and operational efficiencies are maximised to reduce costs.
How we can Help
Our team can help; providing strategy, procurement and project management services as and when you need them. Get in touch with our Retail, Property, & Manufacturing team, to discuss a range of services which might suit your business needs: info@cambridgemc.com.
View our Retail, Property, Manufacturing practice.
Our Services
Cambridge Management Consulting has a team of experts who specialise in the PSTN switch-off and help private and public sector organisations of all sizes. We can analyse your telephony and IT equipment, as well as alarms and other special service devices; and then create a detailed migration plan as well as offering procurement services to keep this plan within your budget.
By outsourcing this process, you can save time and money and also negate the drain on daily resources——allowing your teams to stay focused on daily operations. If you do not have the knowledge and skills in-house to manage this process, please get in touch with Clive or Craig using the form below to discuss your requirements.
Terminology
PSTN: Public Switched Telephone Network - a complex network of copper wires, switching centres, and other infrastructure that has been the backbone of the UK's telephony network since Victorian times.
VoIP: Voice Over Internet Protocol - a technology that allows people to make voice calls using an internet-based communications technology. By converting voice signals into digital data packets, VoIP can transmit conversations over broadband connections and across the internet.
IP: Internet Phone - the digital version of your traditional home telephone. It uses VoIP to transmit your voice over a broadband connection. IP phones can offer a range of features like voicemail, call forwarding, video calls, and integration with other internet services.
Digital Voice: refers to BT's specific VoIP service or more generally to any service that transmits voice over your broadband connection. Confusingly, VoIP, IP and Digital Voice are often used interchangeably.
CP: Communication Provider - an organisation, either private or public, that offers telecommunications services or a mix of information, media, content, entertainment, and application services over networks.
ISDN: Integrated Services Digital Network - a set of communication standards that allow for the digital transmission of voice, video, data and other services over the PSTN network.
ADSL: Asymmetric Digital Subscriber Line - allows for high-speed data transmission over existing copper lines. ADSL is a type of digital subscriber line (DSL) technology that is typically provided from a telephone exchange enabling broadband internet access, video-on-demand, and LAN services . The service is asymmetric in that the broadband speed profile to the premise is higher than that from the premise. Maximum download speeds are in the order of 20Mbit/s (Megabits per second).
VDSL: Very high speed Digital Subscriber Line - a form of DSL technology primarily delivered from street side cabinets delivering very high-speed data rates over existing copper lines. Often referred to as Fibre To The Cabinet (FTTC). VDSL is an asymmetric service, with superior performance when compared to ADSL technologies. Maximum download speeds are in the order of 80Mbit/s.
FTTP: Fibre To The Premises - a fibre connection from a premises to a fibre exchange. Offers superior performance when compared to DSL technologies. Services can be symmetric or asymmetric. Maximum speeds are in the order of multiple Gbit/s (Gigabits per second).
FTTC: Fibre To The Cabinet - a type of digital subscriber line (DSL) technology that delivers very high-speed data rates over existing copper lines, often from street-side cabinets. It utilises fibre optic cables to the main exchange and copper wires to connect to individual premises.
SOGEA: Single Order Generic Ethernet Access - only provides a broadband service rather than a package including a phone line. SOGEA is cheaper because it only provides data.
Useful Links
A Councillors Guide to Project Gigabit: https://www.gov.uk/guidance/a-councillors-guide-to-project-gigabit
https://www.gov.uk/government/publications/gigabit-broadband-voucher-scheme-information
Gigabit Voucher Scheme Eligibility Checker: https://www.gov.uk/government/publications/gigabit-broadband-voucher-scheme-information
Project Gigabit government webpage: https://www.gov.uk/guidance/project-gigabit-uk-gigabit-programme
Virgin O2 guide to the Switchover: https://www.damianhinds.com/sites/www.damianhinds.com/files/2023-10/23%2010%2030%20Virgin%20Digital%20Voice%20Switchover%20MP%20Guide.pdf
Ofcom guide to moving your landline to digital: https://www.ofcom.org.uk/phones-telecoms-and-internet/advice-for-consumers/future-of-landline-calls#:~:text=If%20you%20don%27t%20have%20a%20broadband%20connection%2C%20your%20provider,take%20up%20a%20broadband%20service
BT Guide: How the PSTN Switch Off will Affect my Business: https://business.bt.com/insights/what-is-ip-telephony-pstn-switch-off/
A guide to digital voice: https://www.damianhinds.com/sites/www.damianhinds.com/files/2023-10/23%2010%2030%20A%20guide%20to%20Digital%20Voice%20BT%27s%20new%20home%20phone%20service.pdf
Telecare stakeholder action plan: https://www.gov.uk/government/publications/telecare-stakeholder-action-plan-analogue-to-digital-switchover
Shared Rural Network: https://srn.org.uk/about/
Digital Poverty Alliance: https://digitalpovertyalliance.org/
Government guide for local councils: https://www.gov.uk/government/publications/uk-transition-from-analogue-to-digital-landlines-guidance-for-local-authorities/uk-transition-from-analogue-to-digital-landlines-guidance-for-local-authorities
Telecare National Action Plan: https://www.gov.uk/government/publications/telecare-national-action-plan-protecting-telecare-users-throughout-the-digital-phone-switchover/telecare-national-action-plan-protecting-telecare-users-through-the-digital-phone-switchover
Working Group for Local Authorities: https://www.local.gov.uk/our-support/cyber-digital-and-technology/digital-switchover/working-group
Additional Sources
https://www.ukauthority.com/articles/london-cdo-raises-alert-for-councils-over-pstn-switch-off/
https://www.channelfutures.com/channel-business/pstn-switch-off-set-to-cause-problems-for-businesses
https://www.commsbusiness.co.uk/content/news/charities-urge-clarity-after-pstn-switchover-delay/
https://www.bbc.com/news/articles/c5119g5z4q5o
https://www.commsbusiness.co.uk/content/news/charities-urge-clarity-after-pstn-switchover-delay/
https://www.ft.com/content/df368907-17a8-43cb-9a8e-28be20e6ea7c
Contact - PSTN Deadline Article
Subscribe to our Newsletter
Blog Subscribe
SHARE CONTENT